Full article

The shortest honest answer is this: proof-of-purchase checks are becoming the release bottleneck when verification, approval routing and payment release are treated as separate jobs. In many consumer payout operations, the document review itself is not the slow step. Time is lost in the gaps around it.
That matters because late reimbursement is not just a service issue. It creates rework, produces uneven handling, and leaves teams rebuilding the payment record after release. The practical fix is not mysterious. Put verification in the controlled payment workflow where it belongs, give it one operational owner, set acceptance criteria before cases arrive, and track it like any other release control. If your plan has no owner and no date, it is still a discussion.
The pressure sits upstream of release
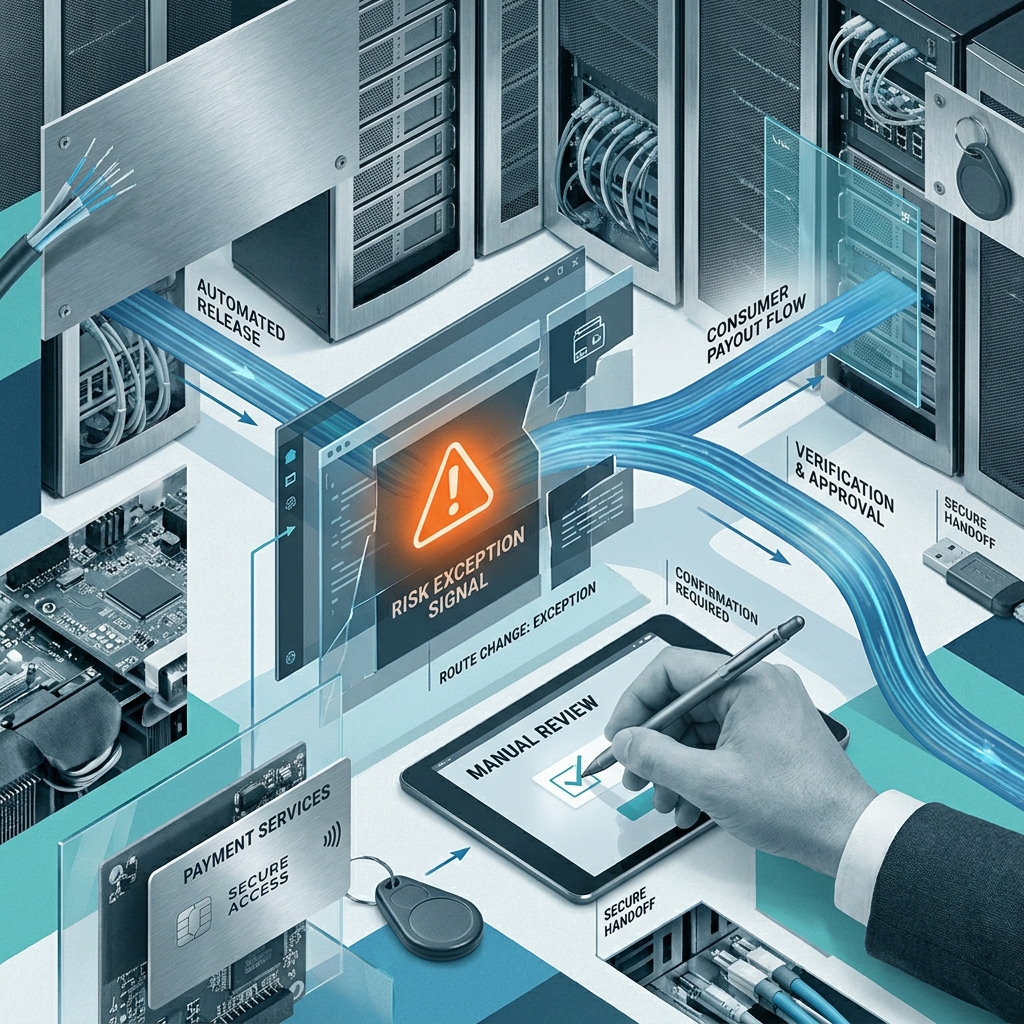
The shift here is operational. A receipt or transaction confirmation arrives through a form, inbox or case record. One team gathers it. Another decides whether it counts. An approver waits for a cleaner file. Payment operations wait for approval. Release status then sits somewhere else again. The proof check may take minutes. The queue around it takes days.
That fits the signal cluster around proof-of-purchase checks. What looks like a document task is really a release-control problem. Loose evidence standards slow approval routing. Slower approval routing lets payment status drift away from the underlying case. The claimant sees delay. The business inherits a weaker audit trail and more back and forth to make the case release-ready.
The pattern is familiar because it is structural. An image is hard to read, so the case is held for follow-up. The follow-up lands outside the live queue. An approver opens the record, finds it incomplete, and sends it back. None of that tells you the claim is wrong. It tells you the operating flow is not holding verification, approval and status in one governed route. Bit tight on time, and a three-day target slides into two weeks through drift rather than a single dramatic failure.
There is a control trade-off underneath it. Release funds before proof is properly validated and pace may improve while reimbursement governance weakens. Push the check too late, after approval, and control exists mostly on paper while rework lands downstream. The cleaner route is to validate once, early, against a standard every team can apply the same way.
What the signal cluster actually tells you
The useful signal is not that teams need more approvers. It is that approval usually moves once the case is complete, legible and decision-ready. Delay builds earlier, between submission and clean verification. That is where the bottleneck tends to form.
The first signal is split ownership. One team collects proof. Finance defines what is acceptable. Compliance sets retention rules. Payment operations own release. On the org chart, that can pass as tidy. In the workflow, it often means nobody owns verification turnaround, nobody maintains the acceptance standard day to day, and nobody owns the date by which a case should be ready for approval.
The second signal is inconsistent judgement. One queue accepts a bank statement screenshot, another rejects it. A receipt passes without the transaction date being checked against the refund window. Cases start bouncing. That is rarely a motivation issue. It is what happens when policy has not been translated into an operational standard that different handlers can apply consistently.
A quick test brings this into view. Check three points in the current route: who owns proof validation, what evidence is required for acceptance, and how long cases wait before an approver sees them. If any answer is vague, the bottleneck is already in the frame.
The implication is plain enough. More approval layers will not fix a weak verification queue. Asking payment operations to clear files faster will not fix it either. At best, that hides the problem for a few days. At worst, it leaves someone reconstructing why a payment was released when finance or compliance comes back to review the case. The path to green starts earlier.
What changes once verification is placed properly
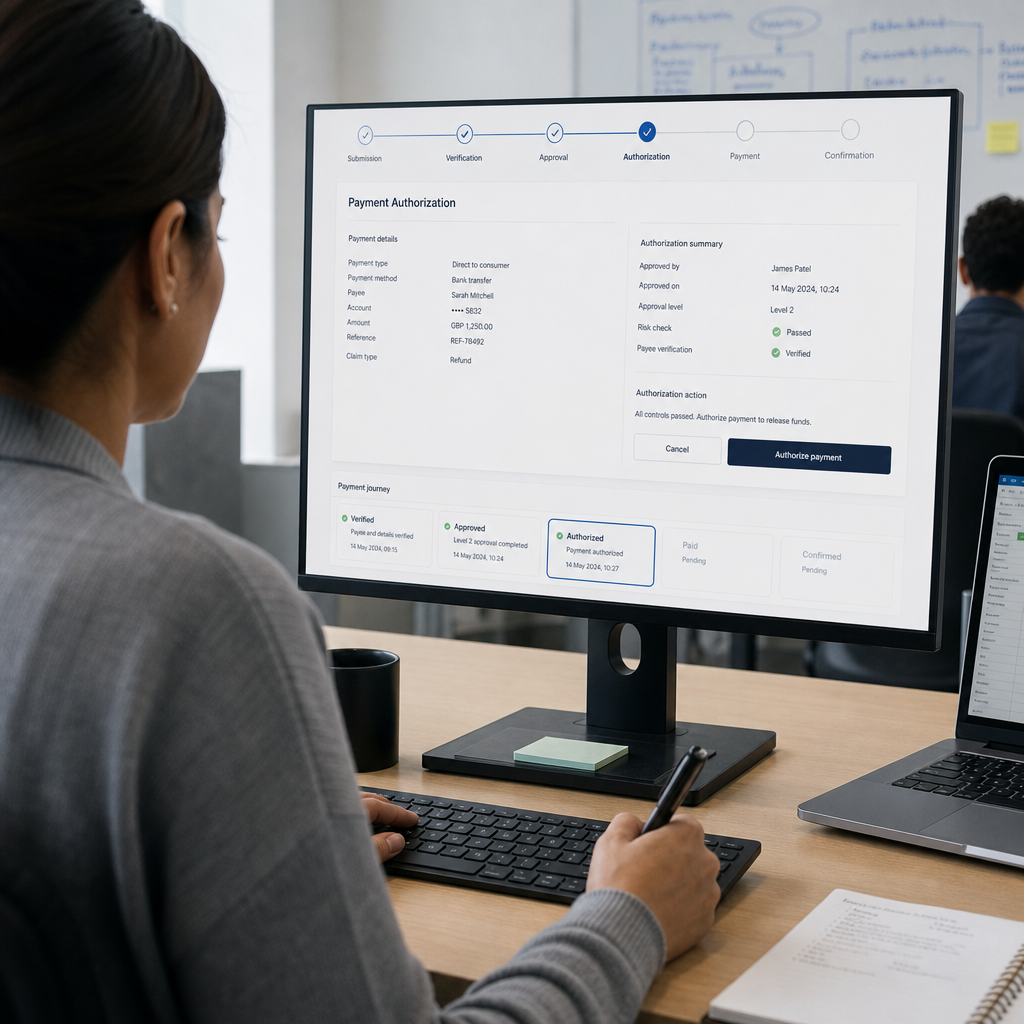
Put proof-of-purchase verification before approval and the workflow becomes easier to govern. The approver gets a case that is ready for decision, not one still trying to establish its own evidence. Payment release becomes more predictable because fewer cases are returned after sign-off. The evidence record stays with the decision instead of being pieced together later from inboxes, notes and spreadsheets.
That only works when verification is explicit. In practice, that means one owner for the queue, one service level, and acceptance criteria visible to everyone handling the case. A case should move to approval only when it includes a legible proof of purchase, a transaction date within the agreed policy window, and a customer identifier that matches the claim record. If one element is missing, the case should trigger a standard exception response with a clear next action.
The gains usually come from cutting rework, not forcing speed. Useful checkpoints include queue age in verification, first-pass acceptance rate, and average time from validated proof to payment release. Those measures show where delay actually sits. They also show whether a change is working, which is more useful than a general sense that the team feels busier than it should.
This is where a governed payout flow earns its place. Each payment should show when proof was received, who validated it, which criteria it met, who approved release, and when funds were sent. That record does two jobs. It gives the claimant a more consistent experience, and it gives the business a traceable account of the release decision when finance or compliance reviews the case later.
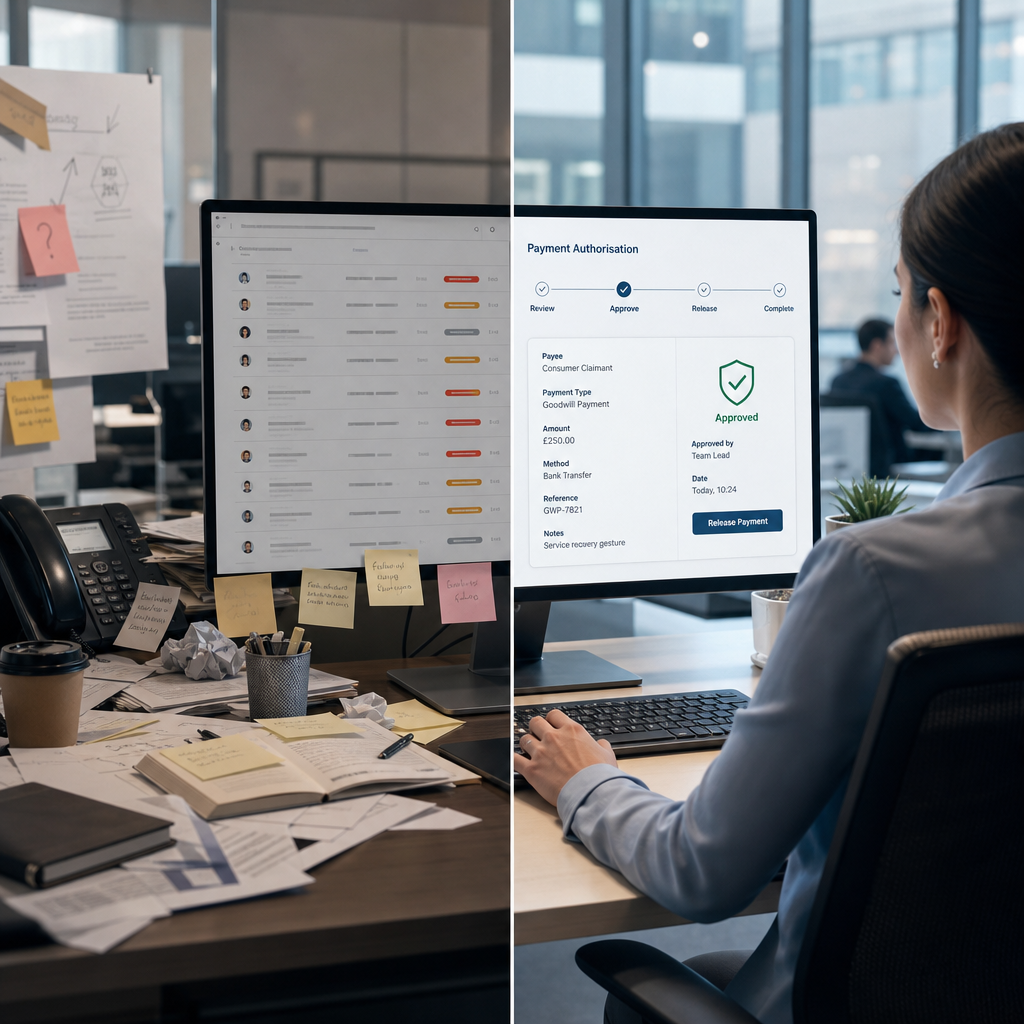
That is the useful comparison. A governed payout control layer keeps verification, approval and payment status aligned in one operating flow. Manual goodwill desks and fragmented payment handling usually break that chain, because the control sits with people, inboxes and side logs rather than with the route itself.
What good looks like for owners, dates and acceptance criteria
If the workflow is going to improve, someone needs to own the next move. A sensible model gives proof validation to one operational owner, while finance owns the policy standard and compliance signs off retention and audit requirements. Those are different jobs. Treat them as one and the verification queue turns into a cross-functional argument instead of a managed step.
The verification owner needs a date-bound target. That might mean reviewing new submissions within one working day and resolving exceptions within an agreed service level. Finance should maintain the acceptance criteria and review them on a fixed cadence when refund windows, campaign terms or product rules change. Compliance should confirm which records must be retained and for how long. Basic, yes. Also the point where drift usually starts.
Acceptance criteria need to be testable. “Valid proof of purchase” is too loose to run an operation on. Better is a checklist a case handler can use without guesswork: the receipt or transaction confirmation is legible, the amount matches the claim value or approved variance, the purchase date falls within policy, and the customer identifier or account reference matches the claim. If a criterion cannot be checked consistently, it is not ready for production.
There is a watchpoint here. Teams sometimes tighten the checklist until genuine claimants are pushed into exception handling for minor issues. That is not stronger control. It is poor calibration. The answer is to separate hard fails from recoverable exceptions, review exception volumes, and adjust using evidence rather than instinct.
The next check worth making
If proof-of-purchase checks are slowing release, map the route from claim submission to funds sent and mark every handoff. Then ask four plain questions: who owns verification, what are the acceptance criteria, how long does a case wait before approval, and how many cases are returned for missing or unclear evidence. The answers usually tell you whether the real issue is volume, policy confusion or queue design.
A useful checkpoint is to measure the age of cases sitting in verification and the percentage that pass first time. If first-pass acceptance is low, the evidence request is probably unclear or the criteria are too loose to apply consistently. If queue age is high but first-pass acceptance is healthy, capacity or prioritisation may be the real problem. Different signal, different action.
The main watchpoint is simple. Teams react to late payouts by accelerating the wrong step. They add another approval route, ask payment operations to clear files faster, or build a manual escalation lane. That can move the queue for a moment. It does not remove the cause. Where proof validation is weak, speed downstream just means the errors arrive sooner.
If you are reviewing Payment Services for this kind of release bottleneck, start with a focused assessment of the handoffs, owners and acceptance criteria around verification. Payment Services keeps verification, approval and payment status aligned in one operating flow, which is the control issue underneath the delay. It can help your team map the current workflow, set measurable checkpoints, and define a practical path to green with named owners and dates. If that sounds like the right next move, get in touch. We will keep it specific, useful and properly sorted.