Full article
Over the last six months, the steady rise in compliance operations hiring has looked less like routine expansion and more like a delivery signal. Teams are adding people to chase sign-off, reconcile versions and prove claims because the underlying approval path is creaking. That is not a criticism of the hires. It is a clue about the system around them.
The practical read is simple: if review volume is rising and your answer is only more manual checking, you are buying short-term cover, not fixing flow. Human judgement still matters. It just should not spend half the week hunting the latest file, checking whether legal saw the right version, or asking where the evidence went.
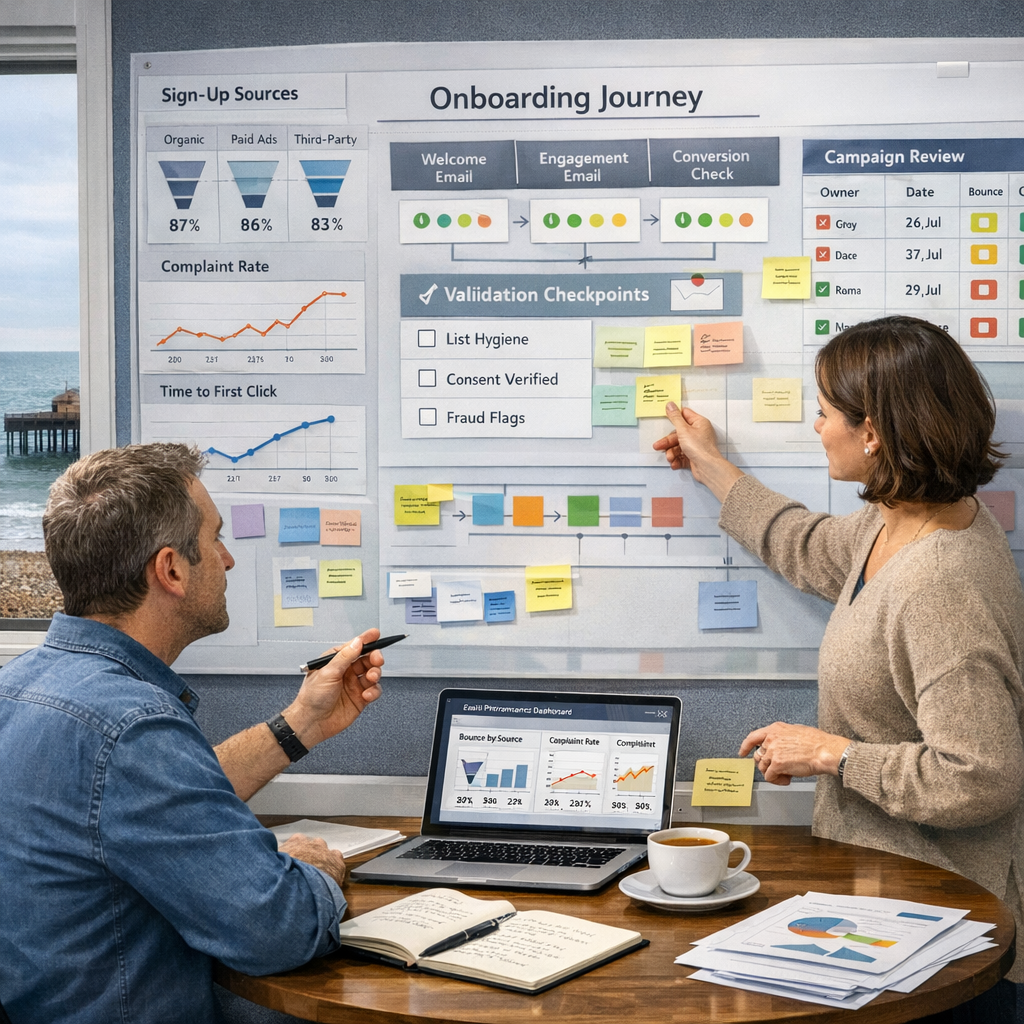
Signal baseline
The pattern in compliance operations roles is fairly consistent. The job spec often centres on tasks that are necessary, but operationally expensive when they sit in email chains and spreadsheets: cross-checking claims against source documents, verifying that terms and conditions are present, and confirming that published copy matches the approved version. That is not strategic policy work. It is manual reconciliation.
That matters because it tells you where the strain sits. When a team runs one large campaign a quarter, a loose approval process can limp along. When the same team is shipping paid social variants, CRM journeys, landing pages and local adaptations every week, it breaks. Yesterday, after stand up, ticket QA-456 was blocked by missing legal sign-off. A quick call with the compliance owner cleared it. New date set for the same afternoon. Useful recovery, yes, but still two hours gone on avoidable admin.
The operational implication is a bit blunt: hiring more checkers may reduce immediate exposure, but it can harden the bottleneck into the process. If your plan has no named owners and dates, it is not a plan, fix it. The same applies here. If the workflow depends on heroic chasing, it is not controlled.
What is shifting
I used to think a clean process document and a tidy RACI would carry more of the load. I was wrong about the effort. The data feed was trickier than expected, and the real problem was not missing rules. It was weak enforcement. Under deadline pressure, people revert to whatever gets the job out of the door, even if that means comments in three places and no reliable audit trail.
The shift is from low-volume, high-stakes approval to high-volume, high-stakes approval. Every asset now carries some mix of brand, legal or performance risk, even the small ones. That changes the requirement. Teams need one review path, explicit sign-off states, visible diffs and evidence attached where claims are made. That is where approval workflow release notes stop being housekeeping and start being useful delivery documentation. They should show what changed in routing, who now owns the next step, what acceptance criteria apply, and how success will be measured.
A sensible checkpoint here is review latency. If you cannot state the median time from submission to approval, broken down by content type or approver group, you do not yet have a baseline. Owner: operations or content lead. Date: within 10 working days of starting the workflow review. Acceptance criteria: one agreed baseline report covering queue age, number of revision rounds and percentage of assets approved on first pass.
Why more hiring often points to workflow debt
More compliance operations headcount can be the right short-term call. If risk is high and the queue is already slipping, you need cover. No drama there. The trouble starts when the role becomes the fix rather than the buffer. Then the organisation quietly accepts that evidence will arrive late, feedback will conflict, and final checks will happen at the end when change is most expensive.
That is workflow debt. You see it in repeated signals: assets waiting on one person’s inbox, reviewers checking screenshots instead of source-linked proofs, and teams unable to explain which version was signed off. Between 14:00 and 16:30 last Thursday, I rewrote the acceptance criteria for a review step after a story kept bouncing back. Tests passed once the edge case around statistical claims without attached sources was covered. Small change, big difference. The queue moved because the rule became testable.
The stronger response is to move checks upstream. Attach evidence before review. Route by risk, not habit. Make version diffs visible so approvers are checking the change, not rereading the whole asset from scratch. Keep the human reviewer in control, but stop making them do filing work. Sorted.
Who is affected
Brittle approval workflows do not just slow compliance teams. Writers wait on ambiguous feedback. Marketing leads lose confidence in launch dates. Programme owners end up reporting risk late because no one can see the real queue. Senior stakeholders often think they have a governance problem at the top, when they actually have a routing problem in the middle.
That is why the owner list matters. For most teams, the first move sits with the Head of Content or Marketing Operations lead, not legal. Their job is to map the live workflow as it actually runs today, including shadow steps. Legal or compliance should then confirm control points, evidence requirements and escalation paths. Product or platform owners need to configure the route and log changes. Three owners, one path.
Use a short test here. By the end of this quarter, can the team answer these three questions without debate: who approves promotional claims, where the source is stored, and what happens if the claim changes after approval? If not, the process is still relying on memory. Risk: uncontrolled rework and delayed release. Mitigation: a single workspace, visible ownership and dated approval states.
Actions and watchpoints
Start with the current-state map, not the ideal-state deck. Owner: Head of Content or Marketing Operations. Date: end of this quarter. Acceptance criteria: document every approval step, average wait time, top two blockers and the systems used at each stage. Keep it honest. If legal reviews happen in PDF mark-up while campaign status lives in a separate tracker, write that down.
Then set a path to green for one bottleneck at a time. Good first candidates are usually evidence capture for claims, conditional routing for high-risk content, and centralised version comparison. If you try to redesign everything at once, you will slow the team and lose backing. Bit tight on time is a normal delivery constraint, not an excuse to skip control.
Watch the adoption risk early. The technical setup is usually the easier part. The harder part is behaviour change, especially where reviewers have used the same habits for years. Mitigation should be boring and specific: one owner for training, one date for cutover, one week of dual-running if needed, and a change log that records every routing adjustment. A fair checkpoint after 30 days is whether first-pass approval rate has improved and whether median review time is down against baseline. If it has not moved, inspect the route rather than declaring the tool the problem.
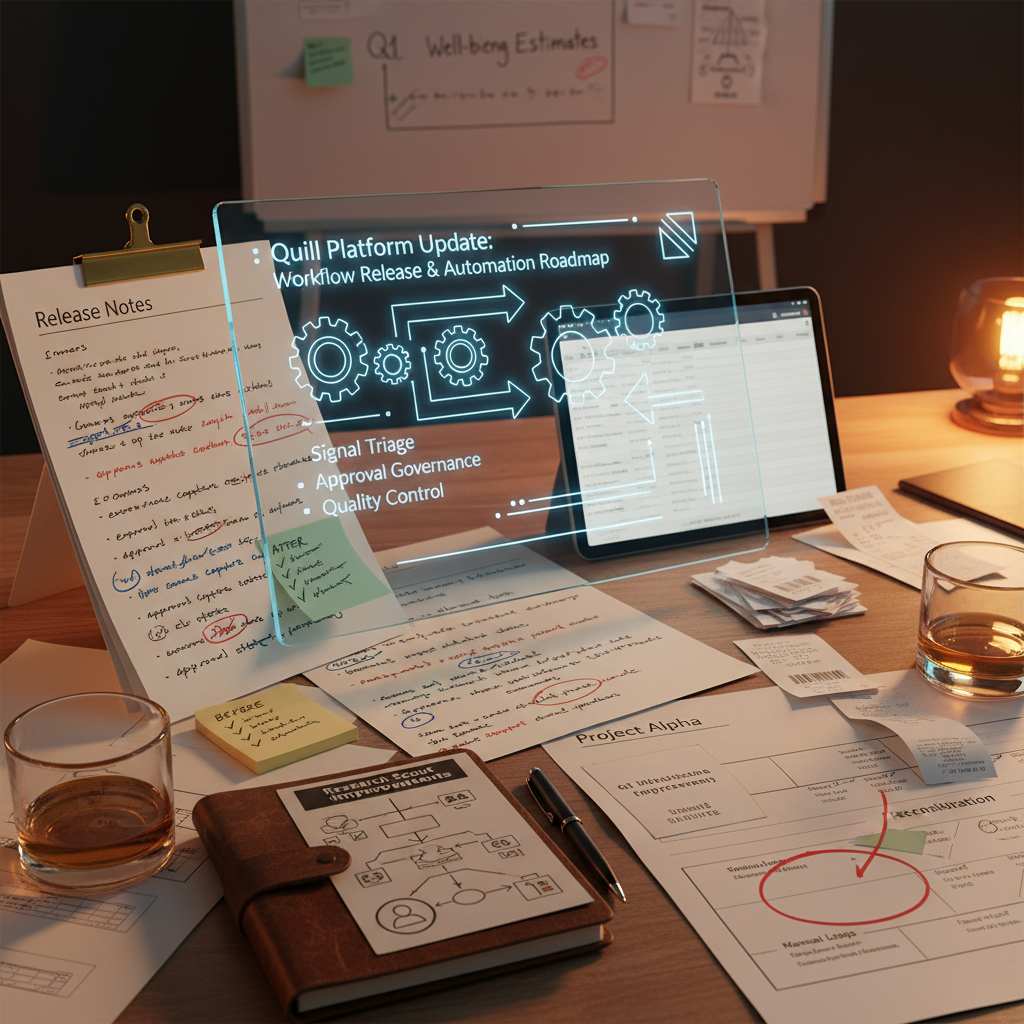
What this means for Quill release planning
For Quill clients, the practical takeaway is that release notes should do more than announce features. They should explain what changed in the approval path, which owner needs to configure it, what teams need to test, and where the audit trail now lives. A good release note is operational: clear on dates, dependencies and acceptance criteria. A weak one is launch theatre.
That is the useful lens on compliance operations hiring. It is a market signal that approval work needs better orchestration, not just more hands in the queue. Quill is built for that middle ground: automation that gathers evidence, shows diffs and routes decisions, while human reviewers keep final control. If you want to pressure-test your current setup, book a guided Quill workspace tour with the automation team. We will map the live approval path, flag the main risk and mitigation points, and show what to configure next so your next release is easier to approve, not just easier to announce.