Full article


Last Thursday, in Canary Wharf, the heating failed while I was reading through AWS compliance notes. Cold room, lukewarm coffee, and a release plan open on the second screen. That’s when the point landed properly: governance shifts, like infrastructure failures, are silent until they freeze your rollout. In regulated UK enterprises, release design lives or dies on whether controls are visible, testable and owned.
This is the practical read for product owners, operations leads and technical decision-makers using the Kosmos software platform in tightly governed environments. The short version is simple enough: AWS is pushing more policy into machine-readable controls, and that changes how Kosmos product updates should be reviewed, released and rolled back. The trade-off is plain. You lose a bit of pace upfront, but you gain auditability when somebody senior asks awkward questions later. Cheers to awkward questions; they usually arrive eventually.
Signal baseline
The baseline signal from AWS is not mysterious. More controls are being surfaced through services such as AWS Config, CloudTrail and Organisations, which means governance is becoming operational rather than documentary. That matters because a release note saying “compliant†is decorative unless the platform can show which control passed, when it passed and who approved the exception when it did not.
For regulated teams, two specifics matter straight away. First, AWS Config rules can be used to detect drift in storage, encryption and regional deployment settings within hours rather than after a manual review at the end of the week. Second, CloudTrail gives you a usable record of configuration changes, which is what audit and incident teams actually need when something has gone sideways. If a platform cannot explain its decisions, it does not deserve your budget.
The original temptation is to frame this as bureaucracy. I’m sceptical of that. The better reading is that AWS has made governance harder to ignore because regulated buyers need evidence, not posture. We saw a version of this in late 2025 when a Kosmos platform update hit ambiguity around data residency interpretation and a financial services campaign slipped by two weeks. Nothing exploded. The release simply could not clear internal sign-off because the evidence trail was too thin. That is the trade-off in real terms: a faster release on paper versus a release that survives compliance review in practice.
What is shifting
The bigger shift is from static policy packs to live enforcement. AWS has been steadily moving governance into APIs, service control policies and policy-as-code workflows. That sounds tidy in a deck. In delivery, it means your release pipeline now has another dependency chain, and some of those dependencies can block rollout without much ceremony.
A concrete example is AWS Organisations with granular service control policies. They can restrict actions by account, service or region, which is useful when you need to support UK data handling expectations and prevent accidental deployment patterns. Useful, but pernickety. If you have not modelled those constraints in your release process, a clean-looking build can still fail at the point of deployment. Between Tuesday and Thursday this week, I tried automating a compliance report and hit missing timestamps in one environment; fixed it with a small Python script pulling directly from AWS Config. Rough edge, simple fix, lesson retained.
For Kosmos release design, the implication is straightforward. Every meaningful product update should carry machine-checkable fields alongside human-readable notes: data residency impact, retention impact, third-party dependency changes, permission changes, rollback conditions. That is more work than pasting polished release highlights into Jira and hoping everyone nods along. It is also far cheaper than discovering after launch that a control owner interpreted the change differently.
I still don’t fully understand why some governance priorities shift so abruptly, but here’s what I’ve observed from UK client work since January 2026: requests about logging scope, regional controls and approval evidence have risen faster than requests about new feature breadth. That is not anti-innovation. It is the market telling you where the real risk sits.
Who is affected
This lands hardest on teams with formal approval chains: finance, healthcare, public sector, insurance, and any enterprise with a legal or security function that actually reads the paperwork. Product owners feel it because release cadence gets dragged into control reviews. Operations leads feel it because rollback plans and access changes become frontline concerns. Technical decision-makers feel it because architecture choices now have governance consequences that are visible earlier.
The audience for this is not abstract either. The ONS quarterly personal well-being dataset and local authority estimates track anxiety and well-being across the UK, and while those series are not a proxy for software governance, they are a reminder that operational pressure is unevenly felt across sectors and places. In plain English: teams already under institutional strain do not benefit from opaque release processes. They need fewer surprises, clearer ownership and evidence they can hand to audit without a minor tragedy in a Teams channel.
Last week, a fintech product owner in Manchester described a release process that slowed once encryption and access reviews were pulled earlier into the cycle. Sensible change, annoying consequence. The cadence dropped, but failed approvals also dropped because the evidence pack was assembled before sign-off rather than after it. In Edinburgh, I watched another team try to manage governance approvals in a spreadsheet after a run of updates. Fine for three changes, over complicated by the tenth. Systems that work for one release often collapse at the exact point the organisation starts to rely on them.
The trade-off here is between local flexibility and repeatable control. Let every team improvise and you get speed in the short term, but inconsistent evidence and brittle audits later. Standardise too aggressively and you create a process nobody wants to use. The answer is usually narrower than people think: standardise the controls, not every sentence around them.
What this means for Kosmos release design
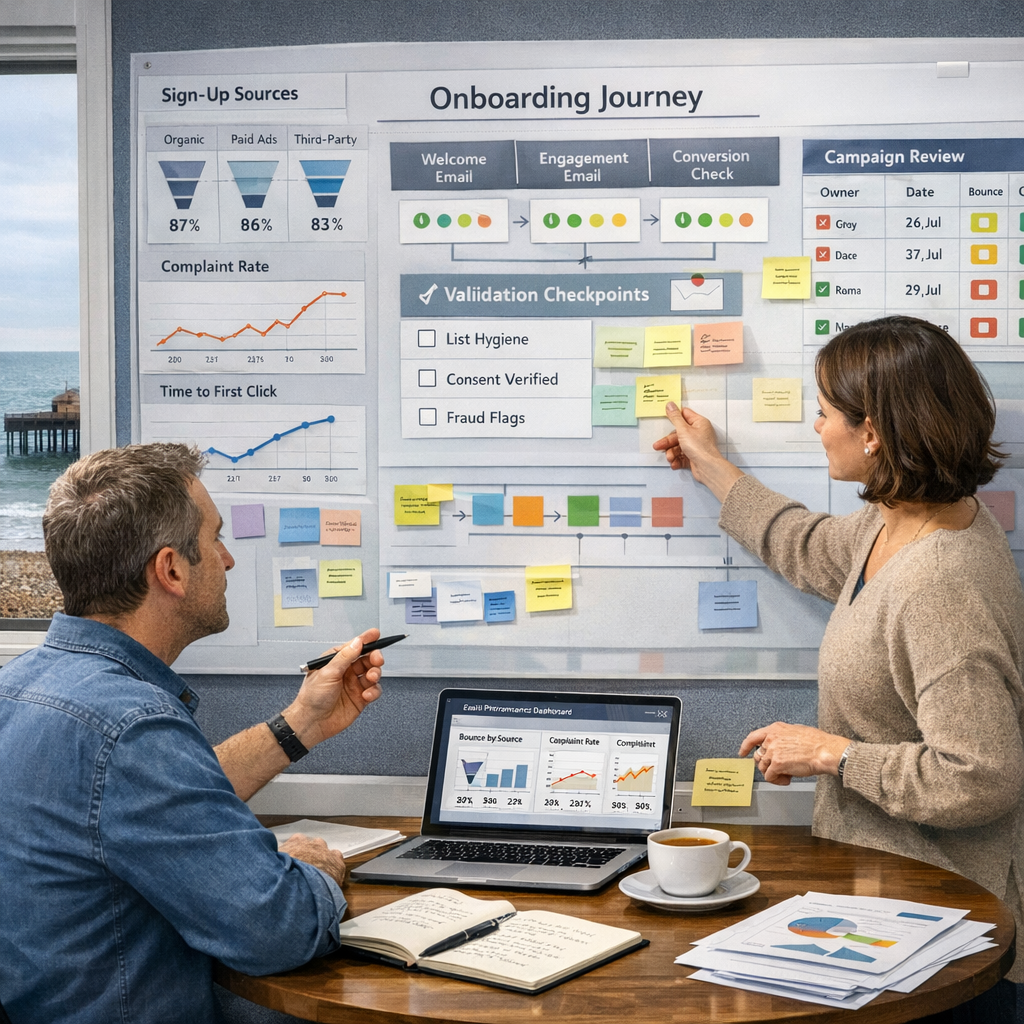
Kosmos product updates in regulated environments should be designed as operational artefacts, not marketing artefacts dressed up in technical clothes. A good release design for Kosmos does four things. It states what changed, shows what governance surfaces are affected, records who approved the risk, and defines how to reverse the change if the assumptions prove wrong.
That means each Kosmos platform update should include named owner fields, control evidence, environment scope and rollback thresholds. If a feature changes data handling behaviour, say so plainly. If it introduces or removes a third-party dependency, log it. If there is no material governance impact, record that too. Silence creates more rework than a short explicit note ever does.
The practical gain is trust. Not fluffy trust. Working trust between delivery, security and compliance teams who need the same facts in different formats. The cost is that release preparation gets a bit heavier. Fine. Better a heavier checklist than a theatrical launch that cannot withstand scrutiny. Automation without measurable uplift is theatre, not strategy.
There is also a sequencing point worth being blunt about. Do not wait until the end of a sprint to ask whether a Kosmos release affects residency, retention or access controls. By then you are negotiating with sunk cost. Put those checks near the start of design and again before deployment. Earlier friction, fewer expensive surprises.
Actions and watchpoints
If you are reviewing the next Kosmos platform update for a regulated UK enterprise, keep the checklist short and evidence-led. Start with release notes that explicitly capture data residency, retention period changes, permission changes, infrastructure dependency changes and rollback conditions. Then tie those notes to what AWS can verify through Config, CloudTrail and organisational policy controls. If the release note says one thing and the logs say another, trust the logs.
Watch the external signals too. The Information Commissioner’s Office and the Financial Conduct Authority both shape how cautious internal teams become, even when the technical change looks modest. AWS service-level or policy updates can have a knock-on effect if they alter assumptions around regional controls or logging coverage. Re-check them before launch, especially if the release touches customer communications, regulated workflows or personally identifiable data.
The practical next step is simple enough. Audit your current Kosmos release template against the controls you already claim to operate. Document one rollback scenario properly. Run one quarterly review where product, operations and compliance all look at the same evidence set rather than three conflicting summaries.
AWS governance signals are not a reason to slow everything down for sport. They are a prompt to build releases that can explain themselves under pressure. If you are weighing how the next Kosmos update should be structured for your own approval chain, we can help you make that decision with proper operational clarity. Have a conversation with the team about your current release flow, where the evidence breaks, and what to fix first; you will leave with a clearer design and fewer nasty surprises at sign-off.