Full article

A valid-looking email address that clears basic checks can still poison your CRM. Most teams treat validation as a typo filter, but the expensive problem is the address that looks correct but is not. The obvious bad entry is rarely the one doing the damage.
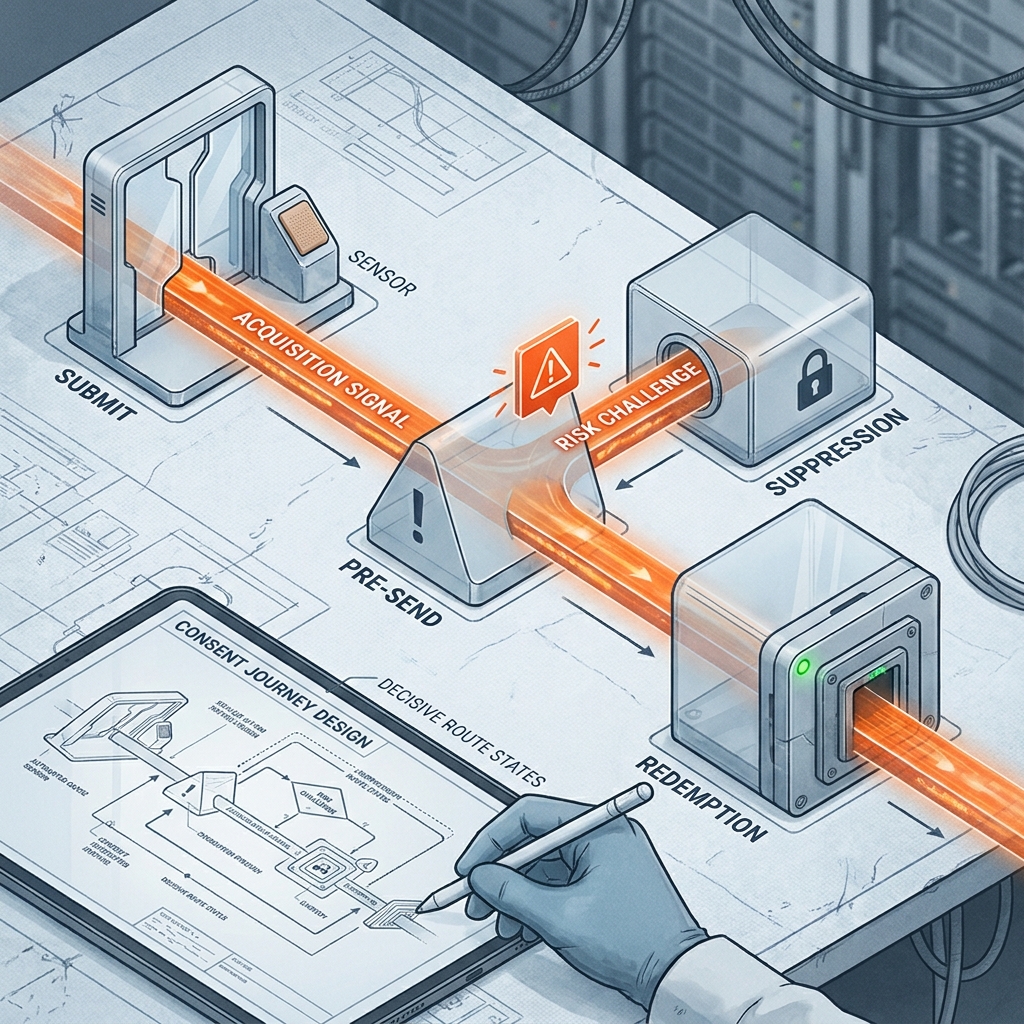
The practical answer is a governed control loop. Check the address at capture, route it according to explicit risk thresholds, monitor downstream metrics, and tune the rules using live bounce, complaint and consent data. This reduces fake enquiries without creating unnecessary form friction.
What you are solving
A bad address inflates list size, distorts attribution and pushes poor records into CRM workflows, creating manual work. If the address bounces or attracts complaints, the cost lands squarely on sender performance.
Toxic data often looks tidy on the way in. A syntactically correct address can still be disposable, role-based or tied to a catch-all domain. Surface-level validation is no longer enough.
There is also a compliance angle. UK GDPR does not declare every weak address unlawful, but a vague consent trail combined with poor database quality makes it difficult to prove what was captured, when, and under which wording. This makes website enquiry quality a governance problem, not just a hygiene issue.
Furthermore, a validation platform must explain its decisions. EVE grades pass, challenge, hold, review or stop outcomes in real time, keeping the reasoning visible. This lets teams tune thresholds and exception handling without slowing legitimate users down. Otherwise, you are not running fraud control; you are decorating a form.
Practical method
A useful validation loop has three working layers. First is syntax and domain checking to stop malformed addresses and disposable providers. Second is mailbox and domain intelligence, assessing catch-all configurations and MX setups. Third is behavioural context, spotting submission velocity, repeated patterns and referral anomalies that suggest low-intent traffic.
The trade-off is straightforward. Stacking checks catches more risk but increases the chance of delaying a form or blocking a genuine user. Speed is critical. EVE runs validation in under 50ms using intelligent caching, supporting real-time decisions without slowing legitimate users down.
Relying solely on a basic validator and double opt-in is clumsy. Double opt-in catches bad records late, often after they have entered your systems, and can suppress decent top-of-funnel enquiries. It is better to validate at the door, reserving extra confirmation only for cases that genuinely justify it.
EVE goes beyond simple checks by applying over 30 proprietary detection methods, including keyboard-walk patterns, entropy analysis and alias unmasking. These identify addresses that are technically plausible but operationally toxic. The goal is not perfect certainty. The goal is to make better routing decisions using evidence, tuning thresholds and exception handling without adding friction.
| Control point | What it checks | Practical use |
|---|---|---|
| Capture validation | Syntax, domain status, disposable patterns | Stops obvious rubbish before it hits CRM |
| Risk scoring | Catch-all signals, role accounts, behavioural anomalies | Routes borderline entries to review or confirmation |
| Feedback loop | Bounces, complaints, engagement, consent records | Tunes thresholds using live outcomes rather than guesswork |
Decision points
Validation is not one rule for every form. A newsletter sign-up, a demo request and a competition entry carry different commercial values and should be judged by different thresholds.
Start with domain reputation. UK marketing teams often apply stricter treatment to recently registered domains during high-risk promotions or referral-led acquisition. A blanket block is rarely the answer. Instead, make a routing decision: allow the record into a lower-priority workflow, require confirmation before a high-value action, or flag it for manual review.
Role-based accounts (like info@ or sales@) require judgement. They are typically poor engagement prospects, but in B2B contexts, they can be legitimate. If a form gates generic content, you might accept them with tracking. For a product trial or sales follow-up, stronger verification is justified.
Catch-all domains are an awkward grey area. Rejecting them outright reduces risk but shuts out real users on normal corporate domains. Accepting all of them is equally flawed. A sensible middle path is to segment them, monitor bounce outcomes, and tighten rules only if evidence dictates.
This is where email fraud prevention teams often misstep. They switch on aggressive settings and wonder why conversion drops without measuring the downstream effect on qualified enquiries.
Common failure modes
The first failure mode is the silent reject. A form refuses the address without explanation, leaving a genuine user guessing. Support tickets rise, and the marketing team learns nothing because no reason code is passed back. Clear feedback matters. Stating 'Please enter a valid work email' is far better than a dead submit button.
The second is the double opt-in cliff. Teams apply confirmation to every journey because it feels safe, only to discover a sharp fall in early-stage conversion. Use confirmation where the risk justifies the extra step, not as a blunt instrument across the board.
The third is failing to close the loop. Validation decisions happen at capture, but bounce data, complaints and engagement are rarely fed back into the engine. A domain that looked acceptable six weeks ago may continue to pass even after its performance has deteriorated. Good routing gets smarter over time; static routing quietly decays.
Teams often trust the neatness of a front-end form more than the messiness of downstream evidence. To fix this, review three signals together every week: hard bounce rate by acquisition source, complaint rate by segment, and the share of accepted records that never progress beyond the first touch.
Action checklist
To improve enquiry quality without adding friction, use this operational checklist:
- Audit the current checks. Document the controls already running at capture: syntax, disposable-domain filtering, role-account treatment, catch-all detection and behavioural scoring.
- Define route outcomes. Decide what happens to accepted, flagged and rejected records for each form. Make the outcomes explicit.
- Match controls to context. A competition form can carry stricter thresholds than a newsletter sign-up. A demo request may justify an extra confirmation loop where a content download does not.
- Connect validation to ESP feedback. Feed bounce and complaint data back into the validation engine so rules reflect live outcomes.
- Keep consent records attached to status. Store capture time, source and wording alongside the validation result so approved records are fully auditable.
- Measure the real trade-off. Track qualified conversion, bounce reduction and complaint movement together. Submission rate alone is a vanity metric.
Website enquiry quality is a continuous control loop, rewarding teams that monitor the system rather than admire the dashboard. Book a frictionless validation walkthrough with our solutions team to look at your current routing logic, see where toxic data is slipping through, and map your next steps.