Full article

Open day demand looks healthy right up until the CRM starts lying to you. One referral source sends a late spike, enquiry volumes jump, and the dashboard says campaign efficiency is improving. Then attendance forecasts miss, nurture emails bounce, and consent records turn patchy. I have seen this often enough to treat every sudden registration surge with mild suspicion and a spreadsheet.
For higher education teams, this is not simply nuisance traffic. It is operational distortion. Toxic sign-ups skew room planning, call-centre capacity, subject demand signals and sender performance. The job is to catch low-quality registrations early without adding so much friction that genuine applicants abandon the form. That is the practical case for email fraud prevention UK: not hype, just cleaner data, better decisions and fewer ghosts in the CRM.
Context
Last Thursday, in a cold office in East Sussex, with local temperatures hovering around 1°C, I was reviewing a familiar admissions pattern. Surface metrics looked lovely: form completions up, cost per registration down, referral traffic broadening. The odd smell came from the email layer. Domain diversity narrowed at the same time that acquisition claims widened. That usually means one of two things: an over-enthusiastic partner source or automated form activity hiding inside otherwise plausible traffic.
Universities are particularly exposed during open day pushes because the registration journey is rightly built for trust and speed. Forms are short, fields are minimal, and the audience spans sixth-form students, parents and mature applicants across a wide range of devices and locations. Sensible design, but with a trade-off: the less friction you apply, the easier it is for synthetic entries, alias farming and throwaway inboxes to blend in.
The wider backdrop matters as well. The NCSC’s Impact of AI on cyber threat from now to 2027, published on 7 May 2025, argues that AI will increase both the volume and quality of cyber threat activity. That does not mean every strange registration is some cinematic AI plot. It does mean bot-assisted abuse is cheaper to run and easier to make look human. Cross-check that with the NCSC’s January 2025 work on forgivable versus unforgivable vulnerabilities and the operational lesson is straightforward: design out common failure modes before the clean-up bill lands.
Tighten too aggressively and you suppress real student interest. Stay too permissive and your CRM becomes a museum of ghosts. That is the trade-off worth managing properly.
What is changing
The first shift is simple: bad registrations no longer arrive wearing a fake moustache. Universities used to catch a fair amount of rubbish through obvious patterns such as disposable domains, gibberish names, duplicate entries from a single IP range or sequential addresses. Those signals still matter, but the more expensive problem now is plausible junk. It comes through legitimate referral paths, uses mainstream mailbox providers and spreads submissions over time.
The second shift is economic. BBC reporting on 14 March 2026 showed renewed scrutiny over whether the government will intervene again on energy bills, with Rachel Reeves saying the Treasury was looking at different options for vulnerable households. That matters because financial pressure changes how prospective students and parents behave. You see more last-minute sign-ups, more shared devices, more comparison activity and more uneven engagement. Some anomalies are therefore perfectly human. A decent detection system needs caveats built in; otherwise teams end up penalising stressed households for behaving like stressed households.
The third shift is structural. Higher education stacks are often stitched together from enquiry forms, CRM middleware, event systems, analytics tags and paid social lead capture. A bot does not need to defeat all of them. It needs one weak endpoint or one partner with sloppy controls. If a platform cannot explain its decisions, it does not deserve your budget. That applies as much to lead sources as it does to validation tools.
The NCSC’s Active Cyber Defence reports from 2019 and 2020 made a broader point that still holds: upstream controls reduce downstream mess when they are applied consistently. Admissions marketing is not national cyber defence, obviously, but the principle travels well. Stop toxic records at capture and you spend less time deduplicating, suppressing and apologising later.
How polluted registration data shows up
The easiest mistake is to frame bot traffic as purely a security issue. In higher education, it is a planning issue first. A polluted open day list affects venue staffing, catering estimates, accessibility support and course-level demand scoring. One burst of fake registrations against a popular subject can push budget and attention towards the wrong faculty for weeks.
The email layer usually exposes the problem before the CRM dashboard does. You might see spikes in typo domains, odd concentration in a handful of consumer mailbox providers, alias variants resolving back to the same base inbox, or bursts of registrations that share behavioural timing but not obvious identity markers. This is where EVE’s validation engine has a practical edge: it combines multiple signals, such as entropy analysis, alias unmasking and behavioural pattern checks, rather than pretending one rule can settle the matter. Even then, probabilities are not certainties. An alias is not proof of fraud. It is a reason to look again.
There is also the consent question. If forms are being filled by scripts or low-quality third parties, the consent trail becomes less defensible. Under UK GDPR, organisations need to show what was agreed, when, and in what context where consent is the lawful basis. A record that says someone opted in is weaker if the surrounding metadata suggests automation, repetition or a mismatch between the referral source and the user journey. Consent compliance is not a legal footer exercise. It starts with input quality.
Between 08:00 and 10:30 last month, I looked at one burst where the failure was suprisingly mundane. A hidden field had been removed during a form redesign, bot friction dropped, and invalid-but-deliverable inboxes flowed straight into the CRM. The fix was not exotic: restore layered checks at the edge, throttle suspicious velocity and require an email confirmation loop before promoting the record fully. Over complicated stacks often fail for underwhelming reasons.
Implications for marketing, CRM and deliverability
Poor-quality registrations damage sender performance long before anyone calls it a crisis. If an open day campaign drives unknown-user bounces, low confirmation-loop completion and weak early engagement, mailbox providers read that as a sloppy acquisition process. They do not much care whether the problem came from a malicious actor, a poor partner source or a hurried landing page build. They care about observed behaviour.
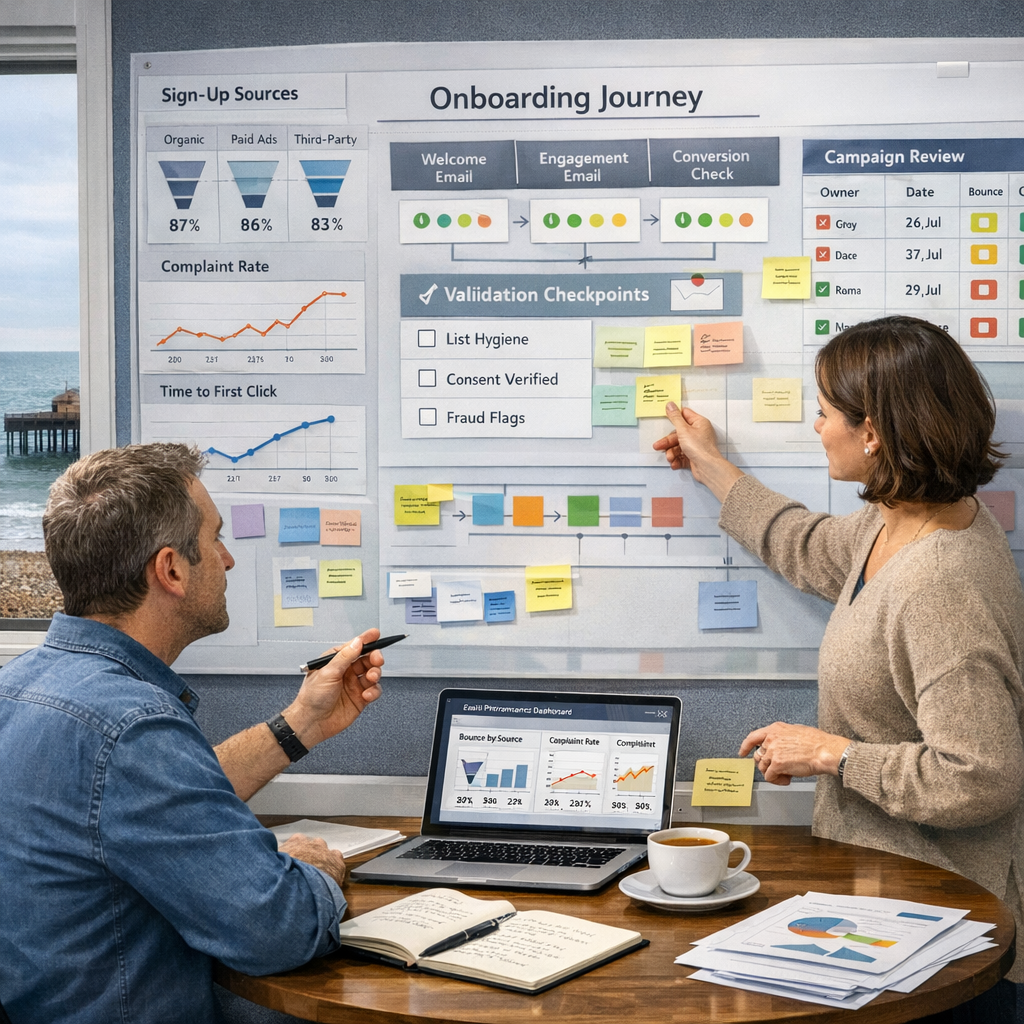
That is why deliverability monitoring should sit alongside source reporting, not in a different monthly deck owned by a different team. I want referral domain, form variant, bounce-code family, mailbox-provider response, confirmation-loop completion and first meaningful engagement in one operational view. When those signals live in silos, nobody notices contamination until the nurture journey underperforms and somebody starts blaming copy.
The second-order problem is measurement. Inflated top-of-funnel numbers make paid media look cheaper than it is, while real attendance looks softer than forecast. Admissions teams then adjust spend or messaging based on false demand. Automation without measurable uplift is theatre, not strategy. If your CRM workflow cannot distinguish a likely student from a highly plausible fake, every polished dashboard built on top of it is suspect.
A caveat, because scepticism cuts both ways: not every bounce cluster is fraud. Students mistype addresses. Families share devices. School and college networks can create strange patterns. The job is not to criminalise messy reality. It is to separate ordinary human mess from patterned abuse quickly enough to protect the campaign.
Actions to consider
Start at the point of capture. Open day forms should validate syntax, mailbox signals and risk indicators in near real time while keeping the experience fast. EVE validates emails in around 50ms, which is quick enough to support a form journey without making it feel heavy. That matters because prevention at the edge is cheaper than CRM surgery later.
Next, rank referral sources by confirmed quality rather than raw volume. Within the first 48 to 72 hours, compare each source against three early indicators: confirmation-loop completion, bounce rate and first meaningful engagement. If a source looks strong on volume but weak on all three, quarantine it for review. Not panic, review.
Then tighten evidence around consent and capture. Store the timestamp, capture point, source detail, form version and session-level metadata where lawful and proportionate. Keep enough to audit decisions, not a hoard of personal data for comfort. EVE’s zero-data-retention model is the right instinct here: preserve privacy while still producing an evidence trail.
Finally, classify failures by consequence. Borrowing the NCSC’s 2025 logic, an unforgivable failure is one that repeatedly allows known toxic patterns into core systems without any compensating control. A forgivable failure is a one-off typo or an ambiguous alias from a real prospect. Design your workflow so the former is blocked or isolated and the latter gets a light-touch verification path. Cheers, that is not glamorous work. It is the sort that protects forecast accuracy and sender reputation when campaign pressure rises.
Open day registrations are one of those systems where small distortions compound fast. A few hundred weak records can misdirect spend, muddy consent evidence and depress email performance across the recruitment cycle. The answer is not more noise and not more friction. It is better instrumentation, sharper source scrutiny and validation that earns its place. If you want a measured view of where your forms, referrals and CRM hand-offs are most exposed, book a frictionless validation walkthrough with EVE’s solutions team. We will show you where toxic data is getting in, and where to stop it without making life harder for genuine applicants.