Full article

AI-led search is sending a different kind of traffic into UK sign-up flows. Volumes can jump quickly, intent can look plausible, and the weak point is often the email field. When that happens, lifecycle teams get hit twice: first in list quality, then in sender performance when campaigns reach inbox providers with a higher share of toxic data.
As it stands, this is less a growth story than an operations test. The Financial Times reported on 13 March 2026 that Nvidia is preparing new inference-focused products as spending shifts from training models to running them at scale. That matters because more AI-assisted discovery means more machine-influenced visits and, in some sectors, more synthetic sign-up behaviour. The practical question is what to do in the first 48 hours after a spike appears.
What you are solving
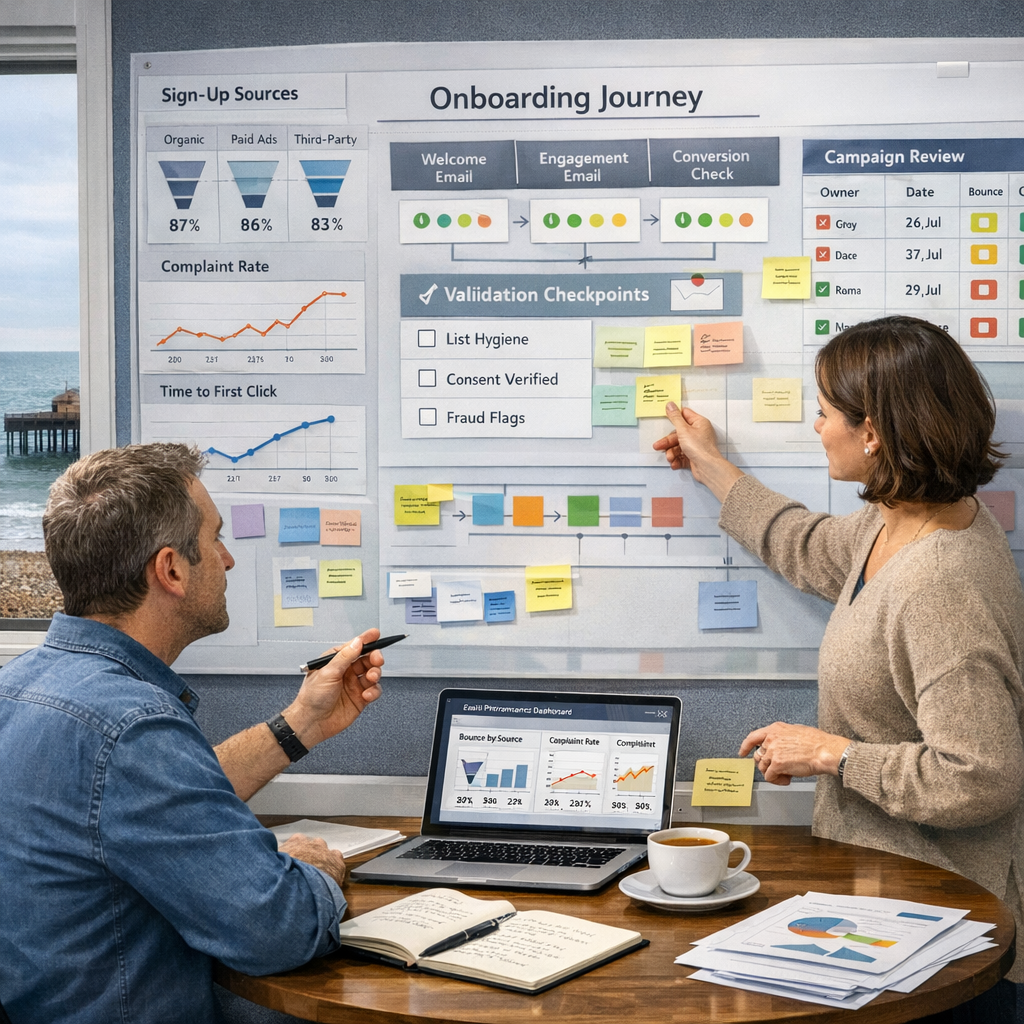
For UK lifecycle teams, the core problem is not simply fake entries. It is decision latency. A sign-up surge arrives, acquisition celebrates, and CRM inherits the clean-up. By then, invalid addresses, disposable domains, typo clusters and consent gaps have already entered welcome journeys, lead scoring and audience syncs.
The wider market context is worth a closer look. BBC News reported on 13 March 2026 that the UK economy was already on shaky ground before fresh geopolitical pressure. On 14 March 2026, BBC News also reported Chancellor Rachel Reeves was considering different options to support households facing rising energy costs. If budgets are tighter and confidence is patchier, every wasted send and every wrongly suppressed real customer carries a sharper commercial cost. You want reachable demand, not flattering numbers that collapse on first contact with the inbox.
That is where email risk monitoring in the UK teams can actually use becomes operationally useful. The aim is to separate likely value from likely noise before automation amplifies the wrong records. A sensible model is straightforward: validate at the point of entry, return a risk signal in real time, and feed that result into routing, suppression and review rules. Not every risky record should be blocked. Some should be challenged, some confirmed, and some accepted with lower downstream trust. A strategy that cannot survive contact with operations is not strategy, it is branding copy.
Practical method for the first 48 hours
The first 48 hours should follow a staged response, not a blanket reaction. In a strategy call this week, we tested two paths and dropped one after the first hard metric came in. A broad suppression option looked tidy on paper. To be fair, it also risked blocking a useful pocket of high-intent users coming from comparison-style queries. The better route was segmented validation with tighter thresholds on suspect patterns.
| Time window | What to check | Constraint | Practical outcome |
|---|---|---|---|
| 0 to 6 hours | Source, campaign, landing page and domain distribution | Do not rely on volume alone | See whether the spike is channel-specific or site-wide |
| 6 to 24 hours | Syntax validity, disposable domains, typo density, alias patterns | Avoid blocking legitimate aliases used by real buyers | Identify pockets of toxic data before welcome sends |
| 24 to 48 hours | Hard bounce rate, email confirmation loop completion, complaint and engagement signals | Need enough send volume for a stable read | Adjust suppression, cadence and review thresholds with evidence |
At the front end, assess whether sign-ups are clustering around newly observed domains, unusual mailbox formats or repeated keyboard patterns. EVE’s validation engine is designed for this sort of job: sub-50ms response time, intelligent caching, and detection methods such as keyboard walks, entropy analysis and alias unmasking. The point is not to fetishise detection for its own sake. It is to catch behaviour that passes a simple syntax check but still looks commercially suspect.
By hour 24, move from entry signals to downstream evidence. Check whether your email confirmation loop is completed at normal rates, whether elevated-risk cohorts are producing disproportionate bounces, and whether engagement differs materially by source. Growth claims without baseline evidence should be parked until the data catches up.
Decision points that matter
Most teams need to make three decisions, quickly.
First, decide where to validate. If your highest exposure sits in lead-gen forms from AI-assisted search journeys, point-of-entry validation is the obvious first move. If the issue is older lists being reactivated by broader search interest, pre-send validation may protect sender reputation faster. The trade-off is simple: entry validation protects database quality earlier; pre-send validation protects campaign performance closer to send time.
Second, decide what to do with ambiguous records. Hard fails are the easy bit. The commercially interesting area is the middle band: valid-looking addresses with elevated risk. The practical option set usually looks like this:
- Accept and route into standard journeys when risk is low and source quality is proven.
- Accept but require an email confirmation loop before incentives, gated content or referral credits.
- Quarantine for review when domain novelty, behavioural anomalies and consent uncertainty combine.
Third, decide how tightly to connect validation to consent controls. Under UK GDPR, marketing teams need a clear basis for contact and a reliable audit trail. Validation does not replace consent, but it does help stop weakly authentic records from contaminating consent logs. EVE’s approach matters here because it pairs audit-ready controls with zero data retention, while making clear that validation results infer authenticity probabilities rather than offering absolute certainty.
A plan looked strong on paper, then one dependency moved, so we re-ordered the sequence and regained momentum. That happens when legal, CRM and paid acquisition are all touching the same funnel. The next move is usually boring but effective: assign one owner for thresholds and one owner for exception handling inside the first day.
Common failure modes
The first failure mode is treating all spike traffic as a win. Source matters. Traffic from a high-intent product page is different from a broad informational query that invites automated summarisation and low-commitment clicks. If you do not separate those paths, your welcome series becomes the testing ground for list quality, which is an expensive way to learn.
The second is over-correcting. Heavy blocking rules can depress legitimate conversion, especially in B2B buying groups or family-account contexts where aliases and forwarding patterns are common. ONS personal well-being datasets continue to track regional variation in anxiety and life satisfaction across the UK. That broader signal is not a direct deliverability metric, but it is a useful reminder that user behaviour is uneven by place and context. Friction added to forms is not neutral.
The third is measuring too late. If your first read on quality comes from monthly bounce reporting, the damage has already spread into sender reputation, audience models and revenue attribution. The faster indicators to watch in the first 48 hours are narrower and more useful:
- Validation pass rate by source and landing page
- Disposable or newly observed domain share
- Email confirmation loop completion rate
- Hard bounce rate on the first welcome send
- Complaint rate and early engagement disparity between low-risk and elevated-risk cohorts
The fourth failure mode is splitting fraud from deliverability as if they are separate departments with separate physics. In practice, they overlap. Toxic data entering through acquisition usually shows up later as poorer inbox placement, weaker engagement and confused suppression logic.
Action checklist
If sign-ups spike after AI-led search visibility improves, the immediate response should be compact and evidence-led.
- Within 2 hours: Segment sign-ups by source, landing page and domain family, then compare against the previous seven days.
- Within 6 hours: Turn on real-time validation at entry for exposed forms, or tighten thresholds if validation is already live.
- Within 12 hours: Flag disposable domains, typo-rich strings and suspicious alias patterns for challenge or confirmation rather than immediate block.
- Within 24 hours: Compare welcome journey performance for low-risk versus elevated-risk cohorts, especially hard bounces and confirmation completions.
- Within 36 hours: Review consent capture language, suppression rules and audit trails so risky records do not gain the same downstream privileges as verified ones.
- Within 48 hours: Decide whether to keep, relax or tighten thresholds based on measurable outcomes, not channel optimism.
The commercial implication is fairly plain. Value appears first where teams shorten the gap between sign-up, validation and routing. That protects deliverability, keeps onboarding fast and gives CRM a cleaner base to work from. If you want a practical read on your current exposure, book a frictionless validation walkthrough with EVE’s solutions team and test your thresholds against live sign-up patterns.