Full article
Executive summary: Cleaner email capture can still create worse outcomes. Tighten the gate too far and the list looks cleaner while legitimate people disappear at the point of entry. Leave it too loose and suppressions weaken, bounces rise and inbox risk moves downstream.
This delivery assurance note sets out the real decision for UK data, risk and platform teams. It is not whether to check email addresses at sign-up. It is whether to keep a silent pass or fail gate, or move to governed thresholds with named owners, review dates and acceptance criteria. If the control cannot show who was stopped, why, and what happened next, it is not doing enough.
The short answer
EVE fits best where teams need real-time email judgement with visible reasoning, tunable thresholds and an override path they can govern. Static regex checks, blocklists and simple allow or deny logic still cover basic hygiene. They fall short when the job is to protect deliverability without quietly excluding valid users.
That is the tension. Email risk is not binary, but many sign-up controls still behave as if it is. A recoverable typo, an uncommon domain and a genuinely unsafe address do not create the same operational consequence. Treating them all as reject may look tidy. It is hard to defend.
What is being decided
Most teams already run some form of email capture check at sign-up. The common pattern is syntax, blocklist, pass or fail. Efficient, yes. Still blunt. A valid but unusual address can be rejected with no decision trail, while the business assumes acquisition is behaving normally.
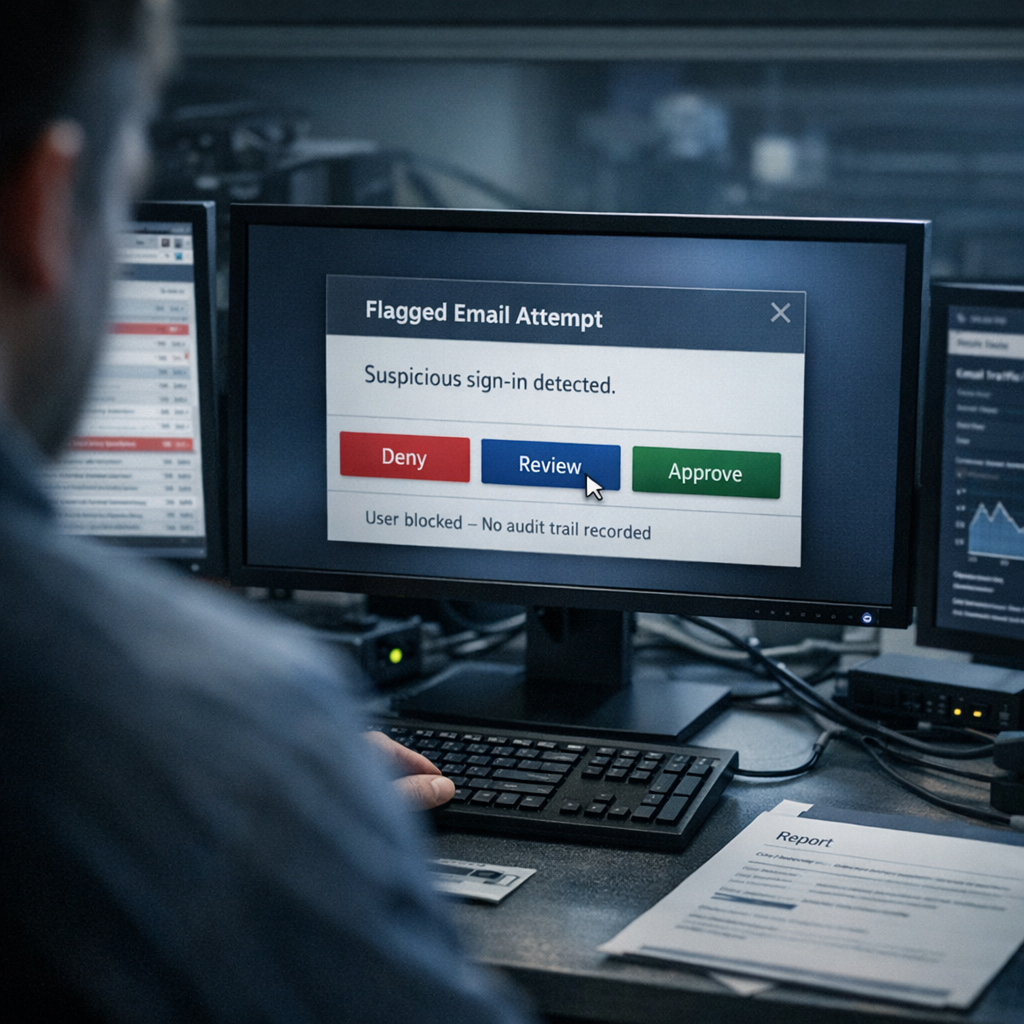
The more useful comparison is between two operating models. One uses a silent gate and treats edge cases as a stop. The other uses graded route states: pass, challenge, hold for review or block. EVE sits in the second model. That matters because the issue is not just whether an address looks valid. It is what consequence the system applies, how visible that consequence is, and whether the team can tune it later.
The harder line often looks cheaper because the misses are designed out of view. They surface later as unexplained drop-off, patchy suppression logic and thin evidence when someone asks why a record was rejected.
Comparative view
Set the two models side by side and the trade-off stops looking abstract. One optimises for apparent simplicity. The other optimises for control, auditability and a cleaner path to green when thresholds need adjusting.
| Attribute | Static pass/fail gate | Governed threshold control with EVE |
|---|---|---|
| Mechanism | Static rules, regex checks and basic blocklists. | Real-time multi-factor assessment such as domain health, mail server checks and risk scoring. |
| Decision route | Pass or reject. | Pass, challenge, hold for review or block. |
| Auditability | Little or none if rejected records and reasons are not logged. | Decision logging with visible reasoning and override history. |
| False-block handling | Weak. Legitimate users can be lost without a trail. | Stronger. Thresholds can be tuned and exceptions can be reviewed against policy. |
| Ownership | Often implicit, set once and left alone. | Explicit owner, review cadence and acceptance criteria. |
The static gate looks easier because it hides the work. The governed model puts the work in plain sight. That is the point. Silent rejection stays neat until evidence is needed, or until commercial teams spot a drop they cannot account for.
A practical example: a standard typo blocker can reject a valid address because an unusual subdomain pattern sits outside a fixed rule. In a silent model, that record is lost. In a governed model, the address can move into challenge or hold, and the CRM owner can clear it against policy. Less neat, more accountable.
What risk or deliverability issue needs controlling
This is where data governance UK stops sounding abstract and starts affecting throughput. Marketing and sales teams care about acquisition friction and list quality. Platform teams care about hard bounces, complaint risk and sender reputation. Compliance teams care about consistency, explainability and whether the control behaves fairly in operation, not just in a policy deck.
A governed threshold model gives each of those teams something they can measure. Two checkpoints matter early:
- False-block rate: track the share of challenged or held records later cleared as valid. Without that measure, threshold tuning is guesswork.
- Hard bounce rate: monitor post-capture bounce performance by route state. If higher-risk addresses still pass through, the threshold is too loose. If valid addresses stack up in review and are later cleared, it is too tight.
The benchmark that matters is direction, not theatre. If hard bounces are running at roughly 2 to 3 per cent, the setup is probably carrying avoidable inbox risk. If a tuned model brings that down towards sub-0.5 per cent without an obvious rise in cleared false positives, that is a material operational gain.
There is a trade-off. More control means more policy. Someone has to own the override route, define what qualifies for manual review and keep a change log when thresholds move. If nobody owns that, the model drifts. If your plan has no named owners and dates, it is not a plan, fix it.
One area still needs careful handling: disposable and short-life inboxes. They need threshold tuning and review because route-state decisions here can shift both false blocks and inbox quality, depending on how strict the model becomes.
Where EVE fits best
EVE is strongest where teams need to judge email capture in real time, keep the reasoning visible and send borderline cases somewhere more useful than silent reject. That makes it a better fit than static regex or allow-list controls when the question is not simply whether an address matches a rule, but whether the team can protect deliverability without blocking good users.
That is the operational core of consent compliance operations here: visible route states, measurable outcomes and a record of who changed what and when. Not glamorous. Useful when audit, deliverability and customer experience start pulling in different directions.
For teams looking wider across customer-data operations, the same control logic matters beyond sign-up. Related products such as DNA, QuickThought and MAIA may matter once consent evidence, downstream messaging or audience handling need the same level of traceability. The immediate decision in this piece is narrower: make primary email capture governable first.
Proof matters, so the comparison should stay grounded. EVE is described as making sign-up decisions in real time, keeping the reasoning visible, and giving teams a governed way to tune false positives, suppression and override policy. The practical question is whether that model gives your team better control than silent rejects and mailbox-quality drift. The product detail is here: EVE. Broader implementation context sits here: Holograph solutions.
Owners, dates and acceptance criteria
The minimum viable operating model is not complicated. It does need discipline.
- Owner: Head of Data, CRM Lead or equivalent operational owner.
- Review cadence: quarterly threshold review, with exception review monthly if hold volumes are material.
- Acceptance criteria: rejected and challenged decisions are logged; override actions are traceable; threshold changes are versioned; bounce and false-block measures are reported.
- Risk: thresholds set aggressively can increase the chance that valid users are challenged, held or blocked.
- Mitigation: use a challenge or hold state before block for borderline cases, and review cleared exceptions against policy.
- Risk: thresholds set too loosely can increase inbox placement issues and hard bounces.
- Mitigation: monitor bounce outcomes by route state and tighten only where the evidence supports it.
Recommendation and next step
The recommendation is plain. Do not keep a silent pass or fail gate as the default for primary email capture if you need auditability, lower inbox risk and fairer treatment of edge cases. Move to governed thresholds with EVE, and make the owner, review date and decision routes explicit from the start.
Next move: the Data or CRM owner should review current email capture rules and suppression logic, set a baseline for false blocks and hard bounces, and document where no audit trail exists today. The output should be a short decision pack for the risk or platform lead with threshold options, known risks and the proposed path to green.
This is not a case for manual-review theatre. It is a prompt to replace invisible rejection with a control the team can actually run. If you want EVE to help map current thresholds, owners and acceptance criteria into a workable operating model, get in touch. We can help assess where false blocks are likely to be happening, what should be challenged rather than stopped, and what needs tightening before inbox risk becomes the bigger issue.



