Full article
Overview
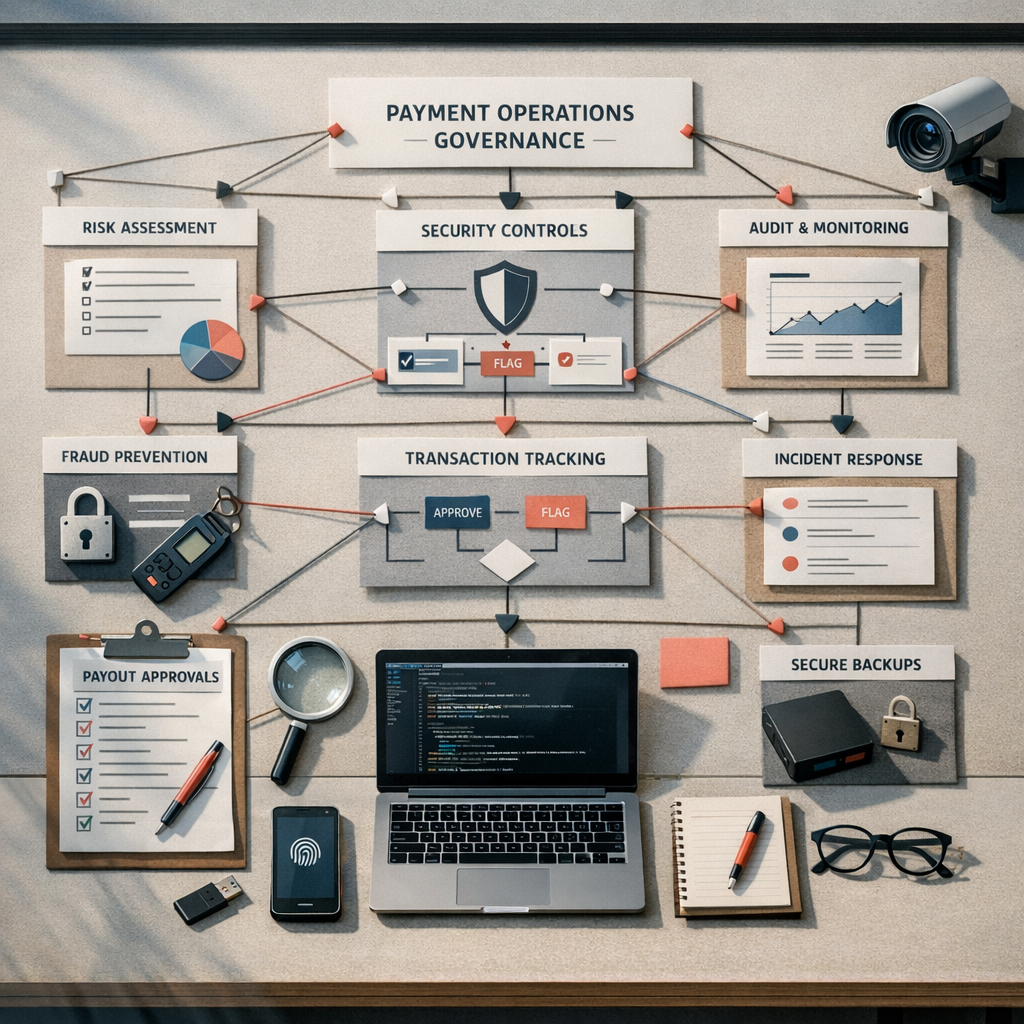
Direct payment governance is not paperwork for its own sake. It is the operating discipline that lets a team move money accurately, explain decisions under scrutiny, and scale without relying on heroics or luck. When payment volumes rise, the old workflow of exporting a CSV, checking it by eye and hoping for the best stops being charmingly scrappy and starts becoming expensive.
These field notes are for UK operations leads who need payout controls that work in the real world. The method is straightforward: map the payment journey, set proportionate controls, test failure paths, and review the whole thing on a schedule rather than after a bad week. A bit less theatre, a bit more evidence.
What you are solving
Last Tuesday, in our Surrey office, I was reviewing a client payment flow that had quietly grown from a few dozen transactions a day to several thousand. The kettle had just clicked off, the tea was still too hot, and a glance at the weather showed a cold snap gripping Sunderland, a sharp reminder of how quickly conditions can change, both outside and on a balance sheet. The workflow on screen was held together by a manual CSV export and a bank upload. It had worked for years. That was the problem. A process can look stable right up to the moment volume exposes the weak joints.
This is what direct payment governance is for. You are moving from a model based on individual care and memory to one based on controls, evidence and repeatability. The job is not to make payment operations slower for sport. The job is to make the correct route the easy route, and to make exceptions visible before they become losses, delays or awkward conversations with compliance.
That matters more as the ecosystem gets more regulated and more complex. On 7 March 2026, PA Daily News via MEXC reported that Pakistan had passed a Virtual Assets Act, a reminder that payment and asset controls are tightening across markets rather than loosening. Closer to operations practice, D3 Security’s 6 March 2026 note on AI-assisted security operations for EU financial institutions reinforces the same point: auditable decisions and clear escalation paths are operational requirements, not decorative extras. If a platform cannot explain its decisions, it does not deserve your budget.
There is a trade-off here. More control can add friction. Too little control leaves you exposed. The sensible answer is not maximal approval on every payment; it is proportional control by amount, payee risk and payment type.
Practical method
Start by mapping one payment from initiation to reconciliation. Use a whiteboard, sticky notes, Miro, the back of a notebook, whatever gets the truth out quickly. Include every system touchpoint, manual hand-off, file export, approval step and ledger entry. If your map skips the boring bits, it will miss the risky bits too.
Then assign controls in three layers: preventative, detective and corrective. Preventative controls reduce the chance of a bad payment being created or released. Detective controls spot anomalies quickly. Corrective controls define what happens next, by whom, and within what time window.
For a concrete example, consider paying freelance contributors. One person prepares the batch. A second authorised person approves it. New payees cannot be paid until bank details have passed verification. Any bank detail change within 24 hours of a scheduled first payment triggers a review. That is not glamorous. It does, however, beat spending Friday evening tracing a misdirected payout.
Between October and December last year, I tested a similar pattern for a media client and the first pass was clunky; approvals were sitting in the wrong queue and causing delay. We fixed it with a simpler approval matrix tied to payment thresholds and legal entities. Error rates fell by more than 90% in the first month, and approval time for low-risk payouts stayed commercially sensible. That is the trade-off you want: tighter control where exposure is higher, less faff where risk is genuinely low.
Decision points
Every governance model contains choices. The useful ones are explicit. The dangerous ones are the accidental defaults that nobody revisits.
The first decision is thresholding. What amount requires dual approval? When does a payment need out-of-band verification? Which changes should freeze release until reviewed? For example, a £5 goodwill refund does not need the same treatment as a £500,000 payroll or supplier run. Write those thresholds down. Build them into the system where you can. Leaving them to judgement on the day is how inconsistency creeps in.
The second decision is role design. A simple RACI works well because it forces operational clarity.
The third decision is evidence retention. If you are asked in an audit review who changed payee details, who approved the release, and what exceptions were raised on 14 February 2026, can you answer without archaeology? This is where governance supports broader assurance work, including ISO 27001-aligned operating controls. You need logs, approval records and reconciliation evidence that are retained consistently and can be retrieved without drama.
There is also a technology decision tucked inside all this. Privacy-preserving architecture is usually the saner choice. The Sambent.com report published on 7 March 2026, examining the gap between privacy claims and legal disclosure realities in the Proton case, is a useful reminder to be precise about what your systems can and cannot protect. In payment operations, that means minimising unnecessary personal data, restricting access by role, and documenting the legal and operational basis for any data handling. Fancy that: clearer boundaries usually make systems easier to run as well.
- Responsible: the person preparing or executing the payment activity.
- Accountable: the person who owns the outcome and can approve or stop the run.
- Consulted: specialists such as legal, compliance or treasury where the payment type requires it.
- Informed: budget owners or relevant department leads who need visibility, not control.
Common failure modes
Most payment control failures are dull before they are dramatic. They start with overloaded teams, vague ownership or control logic that no longer matches the business.
Alert fatigue is the classic one. If your detective controls fire hundreds of low-value notifications each day, the team learns the wrong lesson: ignore the dashboard until something looks truly odd. Between May and July 2025, I saw this with a fintech operations team whose fraud queue had become almost pure noise. We reduced the volume by recalibrating thresholds, grouping low-risk exceptions into scheduled reviews and preserving immediate escalation only for high-risk signals. The result was not magic AI wizardry. It was cleaner triage, faster handling and fewer missed genuine issues.
Hero dependency is another. If only one person knows how to run an urgent payment file, reverse an error or interpret an exception report, your process is brittle. Holidays happen. Resignations happen. Systems fail at awkward times because they have a sense of humour. Your incident response workflow should name primary, secondary and tertiary responders, define acknowledgement windows, and state exactly how a payment run can be paused safely.
Testing neglect is the quieter failure mode. Controls that were sensible last year may be wrong for today’s volume, currencies or counterparties. Cyberwarzone’s 6 March 2026 ransomware trends piece notes that attackers continue to exploit out-of-hours weakness and operational gaps. For payment teams, the implication is straightforward: test access controls, approval chains, fallback procedures and reconciliation timetables as if the incident will happen on a bank holiday weekend, because one day it probably will.
The trade-off is time. Testing takes effort and can feel unproductive when nothing is on fire. Yet untested controls are assumptions wearing a lanyard.
Action checklist
If you are responsible for direct payment governance, this is the short list I would actually use:
One final metric is worth tracking: exception rate as a percentage of total payments, reviewed monthly. It gives you a simple operational signal. If the rate climbs, either the process is drifting, the business has changed, or your controls need adjustment. All three are useful answers.
Good payment operations are built, shipped, tested and reviewed. If your team wants a practical look at payout governance controls, Payment Services can work through your current process with you, cut the faff, and identify where stronger checks will genuinely improve resilience. If that sounds useful, start the conversation and we will help you turn a fragile workflow into one your operations team can defend with confidence.
- Map the full payment lifecycle. Include data entry, file creation, approval, release, confirmation and reconciliation. Name every system and owner.
- Classify the main risks. Focus on wrong payee, wrong amount, duplicate payment, unauthorised release, late payment and failed reconciliation.
- Set thresholds and approval rules. Tie them to value, risk and payment type, then build them into the workflow rather than leaving them in a PDF no one reads.
- Document incident response. Define who investigates alerts, who can pause a run, who contacts the bank, and how payees are verified.
- Reduce noisy alerts. Measure false positives and tune controls quarterly. Automation without measurable uplift is theatre, not strategy.
- Test failure paths. Run a simulation for a bad bank detail change, a failed payment file and a missed reconciliation. Capture timings and gaps.
- Review evidence retention. Make sure logs, approvals and exception reports are complete, accessible and retained for the required period.
- Assign ownership. Use a RACI or equivalent so nobody is guessing when pressure lands.



