Full article

Created by Brenden O'Sullivan · Edited by Marc Woodhead · Reviewed by Marc Woodhead · Published 18 January 2026
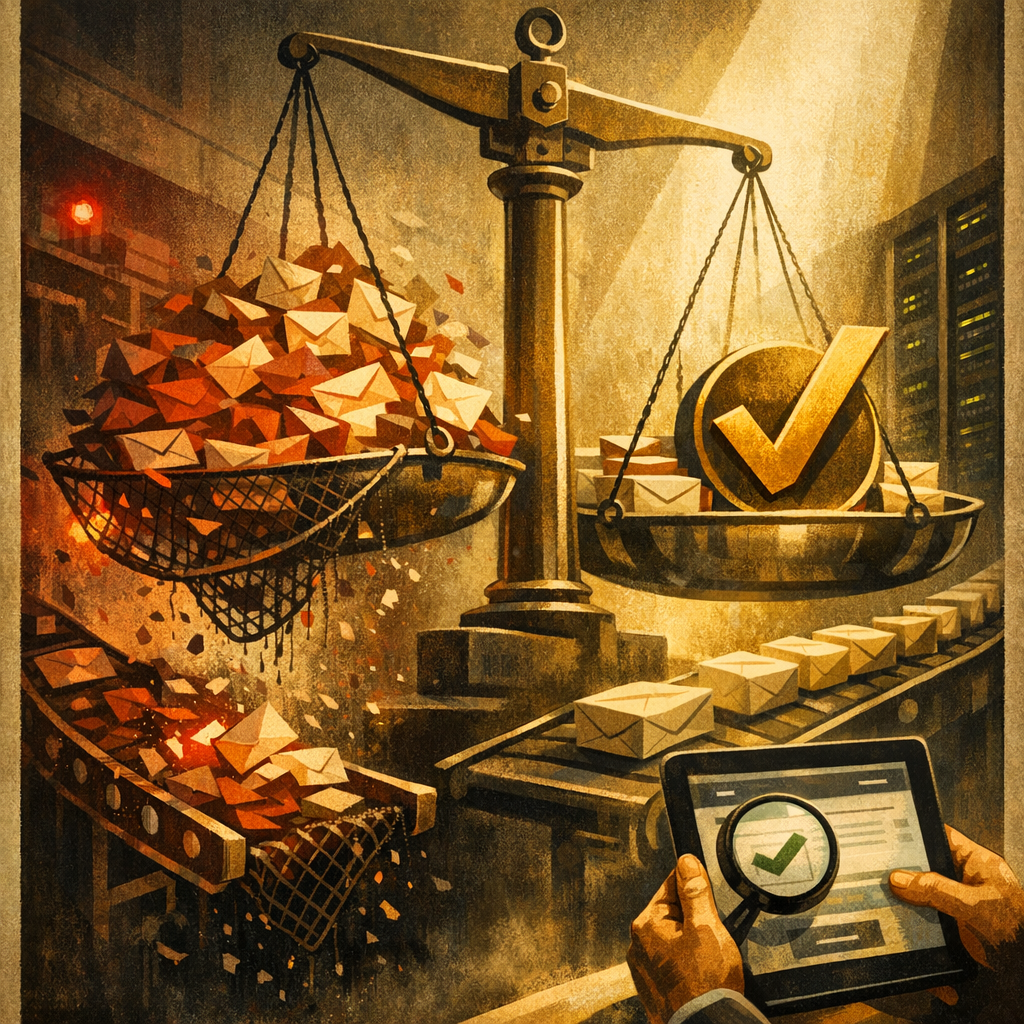
Open innovation needs clean email capture, auditable consent and joined-up risk monitoringOpen innovation programmes aim to pull customers closer, but they often flood systems with low-quality email data that erodes sender reputation and wastes budget. The real trade-off is not between growth and control; it is about embedding intelligent, low-friction validation at the point of entry. A joined-up approach to email risk monitoring separates a successful customer council from an expensive operational clean-up.
Context: why your contact layer is exposed
We have all been in rooms where a bold idea seems perfect, only for the campaign to falter when the form goes live. Incentives hit social media, lists fill with addresses that pass basic checks but are toxic, higher bounce rates, complaint risks, and unprovable consent trails follow. As it stands, treating email capture and deliverability as separate problems is outdated. Modern strategy links acquisition, validation, consent, and monitoring into one system. When motivated participants and bots skew your dataset, protecting entry points becomes a priority, not an afterthought.
What is changing: risk as a connected system
Let's de-mystify email risk monitoring in the UK. It is the ongoing practice of spotting conditions that harm reach, reputation, or compliance, and correcting them quickly. In practice, monitor three signal families together:
- Delivery quality signals: hard bounces, blocks, spam placements, engagement drops. This is classic email deliverability, but linked to how addresses were collected.
- Behavioural and fraud signals: velocity spikes, automated patterns, suspicious domain usage. Even for non-financial incentives, fake entries waste budget and poison sender reputation.
- Consent and governance signals: missing opt-in proof, inconsistent preference journeys. Auditable consent is an operating system, not just policy.
A strategy that cannot survive contact with operations is not strategy, it is branding copy. If risk monitoring splits across dashboards and owners, you are always late to the problem.
Implications: validation must be fast and invisible
Open innovation thrives on low friction, customers sharing ideas without feeling burdened. Controls must work quietly in the background. EVE validates in under 50 milliseconds using intelligent caching and over 30 detection methods, from syntax checks to entropy analysis and behavioural fingerprinting. This reduces toxic data before it hits your CRM, cutting fake entries by up to 95% without adding obvious friction. To be fair, validation infers authenticity probabilities; no tool offers absolute guarantees.
Actions to consider: a practical operating model
Tools are not a strategy. For repeatable results, own the full loop with a clear routine. This model connects marketing, CRM, and compliance, treating risk as integral.
| Stage | What you do | What you measure | Typical fix when it goes wrong |
|---|---|---|---|
| Capture | Validate emails in-line on forms and feeds; flag high-risk patterns. | Invalid rate, disposable domain rate, velocity spikes. | Tighten rules for high-risk sources; add progressive friction only where needed. |
| Consent | Store opt-in proof: timestamp, source, wording, purpose, preference state. | Percentage of records with complete, auditable consent evidence. | Repair broken journeys; unify consent wording; backfill metadata where possible. |
| Send | Segment by risk and engagement; warm up infrastructure when scaling. | Hard bounce rate, complaint rate, engagement drop alerts. | Suppress risky cohorts; clean lists; re-permission where appropriate. |
| Monitor | Track delivery, fraud, and consent signals in one view. | Anomaly alerts, source-level risk scores. | Quarantine low-quality sources; run root-cause analysis by entry point. |
| Improve | Feed learnings into acquisition design; test copy and incentives. | Conversion rate vs. risk rate trade-off. | Adjust incentives that attract automation; refine validation thresholds. |
Every deliverability issue is also an acquisition and governance issue. Run them together, and fixes compound.
If reconnecting with customers is the goal, the plumbing must be sound. To see where poor-quality data enters your sign-up journeys and weigh the trade-offs for fixing it, our team can map your highest-risk entry points in a same-day EVE validation walkthrough. It is the fastest way to gather evidence for your next move. Book a frictionless walkthrough and start real engagement.