Full article

Goodwill payments used to sit in the operational grey area: useful for resolving issues quickly, but often managed with more discretion than discipline. That is getting harder to defend. Recent fraud signals and broader scrutiny of payment governance point the same way: if funds are leaving the business, teams need clear owners, evidence, dates and an audit trail.
The practical implication for consumer payout operations is straightforward. Review the workflow now, before claim volumes rise or an auditor asks awkward questions. The aim is not to slow genuine claimants down for the sake of it. It is to make decisions traceable, reduce avoidable fraud risk and keep a clean path to green when something is challenged.
Context
Two signals matter here. First, in early March 2026, security reporting highlighted fake software downloads being used to spread infostealer malware. That matters because stolen credentials and personal details can be reused in payout claims that look plausible on first pass. If your current control is essentially “the story sounds rightâ€Â, that is a bit tight on time and weak on evidence.
Second, investor and regulatory scrutiny of payment processes continues to tighten, particularly where payment flows sit outside standard billing or payroll rails. The debate around gig worker levies, including the Karnataka proposal that IAMAI asked to delay, is one example of the operational strain caused by changing payment rules. Different market, same lesson: once payment handling becomes more complex, stakeholders want proof of control, not reassurance by email.
What is changing
The old trade-off was speed over formality. For lower-value goodwill payments, many teams accepted light verification because the operational cost of checking everything felt higher than the fraud risk. That balance has shifted. Better-organised fraud attempts, more scrutiny from finance teams and a clearer expectation of auditability mean ad hoc judgement is no longer enough on its own.
In practice, that means three changes. First, identity and evidence checks need explicit acceptance criteria. Second, approval thresholds need to be defined by value and risk; a £50 gesture and a £5,000 exception should not travel through the same route. Third, the system of record needs to show who made the decision, on what evidence and on what date. Yesterday, after stand up, ticket PAY-123 was blocked by a fraud-check dependency. A quick call with Sarah in verification cleared it, and the new payment date was set the same morning. A useful reminder: a control is only helpful if it catches something real and gives the team a workable route forward.
Implications for payout teams
The first implication is financial. If compromised credentials are being used to submit claims, weak verification creates a direct route to avoidable loss. In one client review completed in Q4 2025, a manual goodwill process with no multi-factor verification produced a modelled fraud exposure above £250,000 per quarter. The second implication is governance. Auditors, investors and internal risk teams are less interested in whether a process feels sensible and more interested in whether it can be evidenced. If the record sits across inboxes and spreadsheets, the organisation will struggle to show consistent control. The third implication is operational. Teams often bolt on extra checks after an incident, then wonder why queue times climb and claimant satisfaction drops. If controls are added without clear routing and owners, legitimate cases slow down with the bad ones.
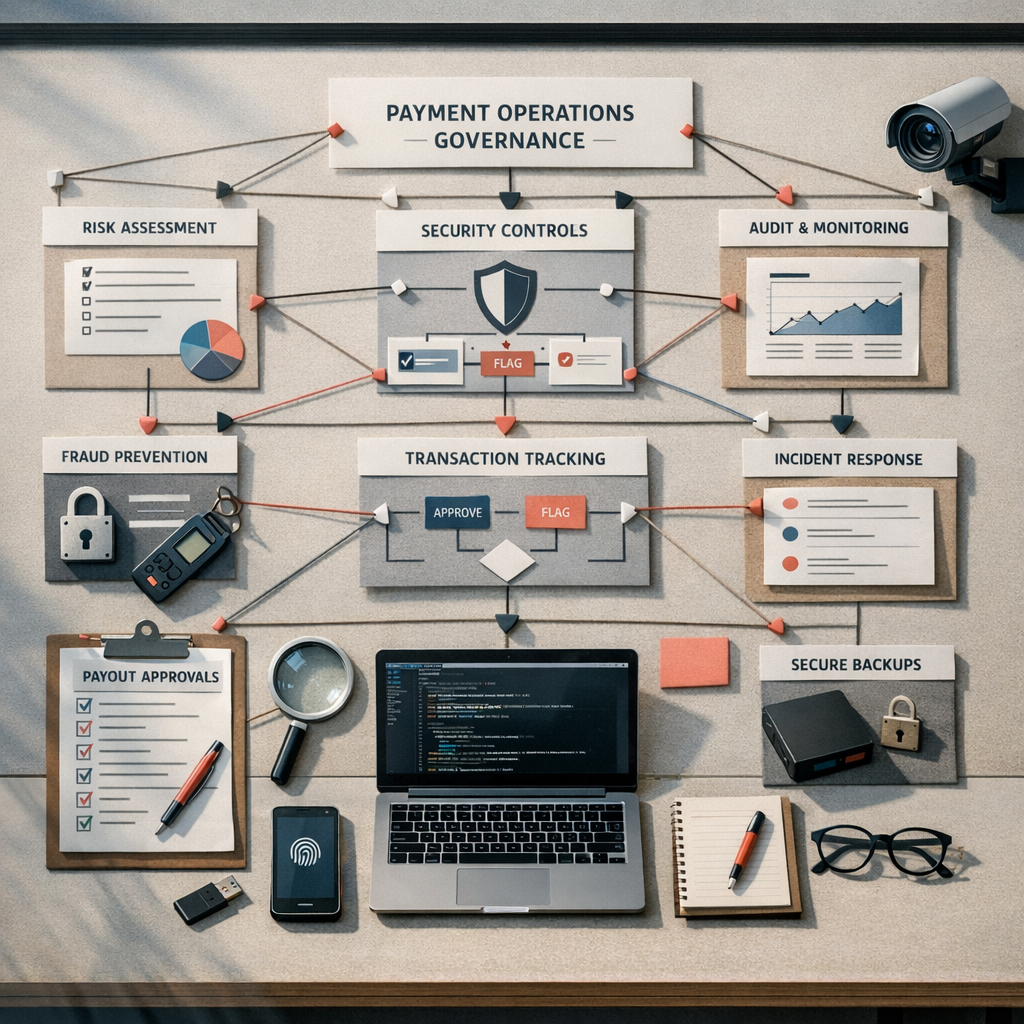
What good looks like
A defensible payout process is not the fanciest one. It is the one that can be followed consistently under pressure. For most consumer payout operations, that means a workflow with named owners at each stage, decision thresholds by value and risk, evidence requirements that can be checked quickly, and a case record that survives audit without detective work. A practical baseline would include identity verification before payment release, dual approval for exceptions above an agreed threshold such as £500, and automatic logging of evidence, approvals and amendments. Add a simple change log as well. If a policy moved on 1 June 2026, you want to know which cases used the old rule and which used the new one. Cheers to anyone who has had to reconstruct that from three inboxes and a spreadsheet tab called “final_v2â€Â.
Actions to consider
If your plan has no named owners and dates, it is not a plan. Fix it. Here is a sensible delivery starting point.
- Document the current and future-state process. Owner: Head of Operations. Date: 30 June 2026. Map the workflow from first claim to disbursement, including every decision gate and hand-off. Acceptance criteria: one version-controlled process map, one risk log, one agreed threshold matrix for payout value and approval level.
- Set control thresholds and evidence standards. Owner: Finance Controller with Legal support. Date: 15 July 2026. Define what evidence is sufficient for common claim types and when enhanced verification is mandatory. Acceptance criteria: policy signed off, exception route defined, sample audit of 20 historical cases completed against the new rules.
- Move case handling into a central system of record. Owner: Head of IT. Date: 31 October 2026. The system should log all user actions, store evidence securely and support reporting on claim volume, average handling time, and suspected fraud rate. Acceptance criteria: full audit log and role-based permissions.
- Test the claimant journey after controls are added. Owner: Head of Customer Service. Date: first review by 31 August 2026. Add clear messaging for evidence requests and publish response time expectations. Measure completion rate and post-case satisfaction to ensure genuine claimants are not facing avoidable drop-off.
Risks and mitigation
The main risk is over-correcting. Teams see fraud headlines, add friction everywhere and create a queue they cannot clear. Mitigation: tier controls by payout value and risk, and review the metrics monthly. If low-value cases suddenly take twice as long, the process needs adjusting. The second risk is under-owning the work. Process redesign that sits vaguely between Operations, Finance and IT tends to drift. Mitigation: assign a single delivery owner, keep a RAID log, and review progress against dates every fortnight. The third risk is weak evidence quality. Even with a new tool, poor acceptance criteria produce inconsistent outcomes. Mitigation: run a sample review of closed cases each month, check whether evidence matched policy, and update guidance where needed.
Goodwill payments are still useful. They help resolve issues and protect customer relationships. But they need the same clarity you would expect anywhere else funds are being released: owner, date, evidence, and an audit trail. If you want a clear read on where your payout process is exposed and what a practical path to green looks like, have a word with Holograph. We can help you map the workflow, tighten the controls and keep the claimant experience workable. Sorted.