Full article

Created by Marc Woodhead · Edited by Marc Woodhead · Reviewed by Marc Woodhead
When should an email rule stop a legal enquiry, and when should it steer it somewhere safer? In regulated intake, this isn't a small technical choice. Email validation sits on the boundary between data quality, client care and operational noise.
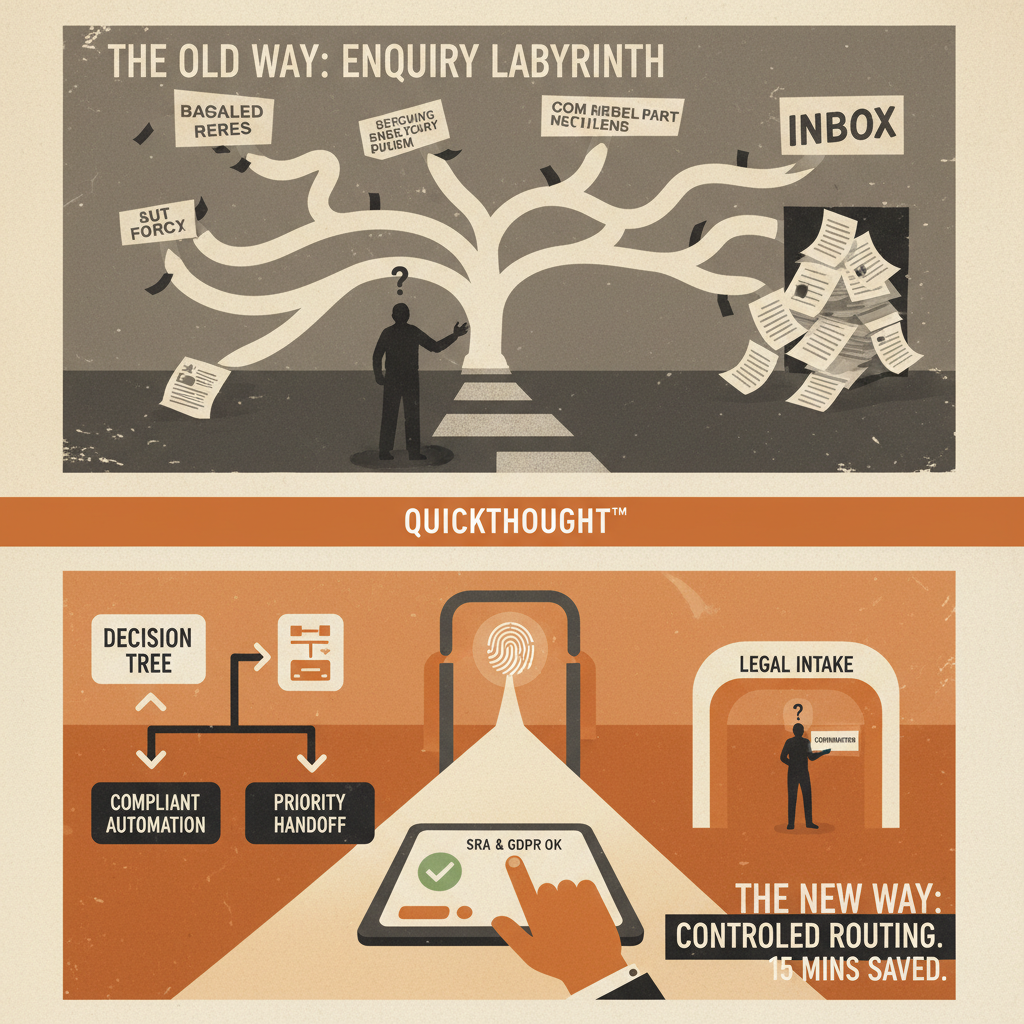
Blanket blocking is usually lazy design. A sharper approach decides in advance which signals justify a hard stop, which warrant a warning, and which should reroute a person to a more suitable path. QuickThought inside Kosmos provides governed decision trees, measurable outcomes and an auditable chain of reasoning.
Decision context
Email validation is often treated as a spam problem, but in legal intake it's a qualification and routing problem. A free email address isn't, by itself, evidence of low intent. In family law, employment disputes and housing matters, personal accounts are often a private, necessary choice. Blocking them outright may reduce junk but can also shut out legitimate enquiries.
This trade-off is critical in legal services. Block too early, and you don't just lose a lead; you lose the chance to triage for urgency, vulnerability or compliance needs. Last Thursday in our London office, I watched a run of enquiries stall after an over-tidy validation rule was switched on. The drop-off line on the dashboard turned sharply, making the trade-off visible: cleaner data at the top of the funnel came at the cost of cutting off real people before the firm had even assessed their fit or urgency.
We've seen firms tighten validation rules only to watch viable enquiries fall, while spam improves only modestly. A better approach keeps personal domains in play but routes higher-risk submissions to a secondary verification step. In these cases, qualification holds up better and the review workload stays manageable.
Options and trade-offs
Most firms have three realistic options: block, warn or reroute. The mistake is to assume one is universally correct; the right choice depends on the signal, matter type and operational support.
| Option | What it does | Likely upside | Main trade-off |
|---|---|---|---|
| Block | Stops submission when a rule is triggered | Reduces obvious junk and duplicate handling fast | Highest risk of losing legitimate enquiries |
| Warn | Flags risk and asks the user to confirm or correct details | Improves data quality without an immediate hard stop | Still adds friction and needs careful wording |
| Reroute | Sends the user to a safer or more suitable path | Preserves intent while containing risk | Takes more design work and stronger governance |
Blocking makes sense when the signal is strong and the downside of proceeding is clear. Disposable email domains, malformed addresses and known bot patterns are good candidates. The cost is bluntness. A block rule is easy to deploy but hard to refine once internal teams get used to the apparently clean data.
Warnings are useful when confidence is lower, for example, if an address contains clear typing errors or the domain looks unusual. They can recover honest mistakes and reduce false negatives. However, if a warning doesn't measurably improve completion or correction rates, it's just a polite delay.
Rerouting is the strongest choice when risk is contextual rather than absolute. It might mean sending an out-of-hours personal injury enquiry to a call-back queue, or a vulnerable user to a simpler form with fewer free-text fields. The gain is continuity, but the alternate path must be real, staffed and logged.
Risk and mitigation
The right question isn't “How do we stop bad emails?” but “What harm are we preventing, and what is the least disruptive control that works?” This framing helps manage four key risks: false rejection of good prospects, false acceptance of junk, compliance failures, and the operational drag of a growing review burden.
Domain-only logic is often the problem. Between 2 pm and 4 pm last Tuesday, I tested a validation setup that was flagging roughly 30% of enquiries as risky. On paper, this looked reassuring. But too many were ordinary personal addresses attached to plausible legal queries. By changing the rule to combine email signals with enquiry context and submission time, we cut false positives by about half. The evidence against domain-only logic is usually sitting in the logs.
This points to a practical mitigation pattern:
- Use hard blocks only for high-confidence technical failures or obvious abuse.
- Use warnings where correction is plausible and useful.
- Use rerouting where the real issue is suitability, urgency or safe handling.
Clarity is also crucial. If you reroute, say why in plain English. “We need to handle this differently to protect your information” is better than a cryptic error. Auditability is the other half. A firm must be able to show which rule fired and why. This is where structured decisioning creates a visible chain of reasoning, which matters when compliance or operations teams review edge cases.
Recommended path
The sensible default is to accept intent, then route according to risk. This means a tiered model.
First, use a small hard-block layer restricted to malformed addresses, known disposable patterns and automation signals. If your block list grows weekly, your upstream design may be poor.
Second, build a warning layer for recoverable mistakes like typing errors. Measure the correction and completion rates. If users aren't recovering, simplify the warning or remove it.
Third, invest most of your effort in rerouting logic. This is where intake qualification becomes useful. Pair the email signal with at least one other factor: matter type, an urgency cue, time of day or vulnerability language. A free email address with an urgent plea at 9:40 pm should be handled differently from a generic commercial query at 11 am.
Rerouting takes more design work than blocking, but it produces fewer avoidable losses and stronger audit evidence. In Kosmos, QuickThought supports this with governed decision trees where rules can be versioned, reviewed and tied to specific outcomes. If the model changes, the rule changes with it.
Case comparison
Consider two firms handling similar enquiry volumes. Firm A blocks all free email domains in the name of efficiency. Its inbox is cleaner and the website looks stricter. Staff feel safer. But then the cracks show: lead loss rises, complaints about inaccessible forms appear, and urgent personal matters arrive late by phone because the original web route failed.
Firm B takes a more considered route. It blocks only clear technical failures, warns on likely correction cases, and reroutes context-heavy enquiries into structured follow-up. Completion rates stay healthier, lead loss is manageable, and the team has an auditable record of why certain paths were triggered. Firm B has more moving parts and more implementation overhead, but in regulated intake, rigid simplicity often creates the very risk it claims to avoid.
When reviewing your validation rules, the question isn't whether to be strict, but where strictness belongs. Holograph helps build this logic into your intake journey, so teams can qualify and route enquiries without collecting more data than needed. This creates an evidence trail for every decision. If you want to see how this would apply to your website, talk to Holograph team. We can map the block, warn and reroute thresholds against your real enquiry flow, not an imaginary perfect funnel.