Full article

Sign-in data holds the potential for swift audience activation, but ambiguous consent permissions commonly block progress. DNA resolves this by imposing a governed workflow from source to segment, cutting approval cycles and rework for UK CRM teams.
What you are solving
Activation stumbles when identity, consent, and destination readiness fail to sync. DNA bridges these divides, guaranteeing that traceable consent underpins reusable segmentation, moving beyond weak governance.
Practical method
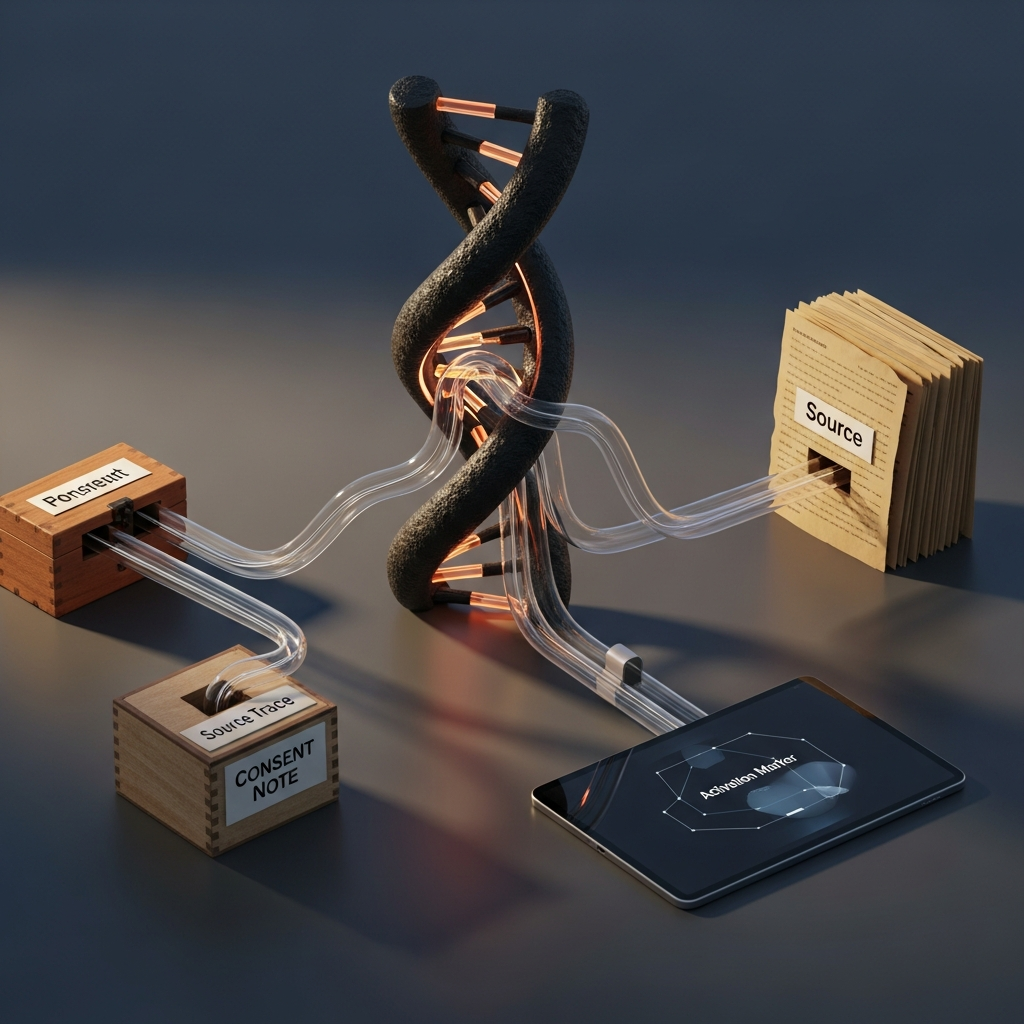
Define the chain: source signal, consent state, identity key, segment rule, destination condition. Clarify each step to prevent delays. DNA enforces this workflow:
| Checkpoint | What to confirm | Why it matters commercially |
|---|---|---|
| Source | Which sign-in event or profile update created the signal | Reduces dispute over whether the audience is based on current behaviour or stale profile data |
| Consent | Permission type, collection point and usable purpose | Cuts approval loops and lowers the chance of suppressions being missed |
| Identity | Which identifier is used across CRM and destination tools | Improves match confidence without over-stitching unrelated records |
| Rule | Inclusion and exclusion logic in plain language | Makes QA and stakeholder sign-off faster |
| Destination | Channel-specific constraints, refresh timing and schema | Avoids rebuilds when a platform cannot accept the data shape supplied |
Focus on sufficient identity confidence for the task, not perfect single customer view. Pair comparisons help balance timeliness and governance.
Decision points
Key decisions include triggering timing, identity matching breadth, and ownership. Direct triggering may be fast but risky with patchy consent; deferred qualification can support governance. Broader matching expands volume but can weaken trust if provenance is unclear. Assign clear ownership for definitions and changes. DNA preserves lineage so downstream users avoid reconstructing intent.
Common failure modes
Avoid binary consent labels when purposes vary. Prevent destination drift by documenting constraints early. Resist over-complication; simpler rules with clear evidence are more defensible. Consistency within use cases is crucial to avoid bespoke negotiations.
Action checklist
Apply this checklist to plan sign-in data activation:
- Define the sign-in signals that may be used for activation, and separate them from service-only or operational events.
- Record the consent state with collection context, not as a generic yes or no field.
- State which identifier underpins the segment, and where that identifier can and cannot be matched downstream.
- Write inclusion and exclusion rules in plain language alongside the technical logic.
- Document destination-specific constraints before building the audience, especially refresh timing and schema requirements.
- Assign a named owner for rule changes, approval and release evidence.
- Keep forms simple where data capture is involved, include opt-out clearly, and avoid collecting fields that do not affect the activation decision.
Result: reduced approvals, minimal rebuilds, increased confidence. Prioritise standardised proof packs instead of ambiguous logic. When sign-in data hinders activation, reinforce the chain. Contact DNA to plan the next step.
If this is on your roadmap, DNA can help you run a controlled pilot, measure the outcome, and scale only when the evidence is clear.